Bluetooth HID delivers driverless interaction for keyboards, mice, gamepads, and similar devices over a wireless link by reusing USB HID descriptors and the report model. It primarily addresses three core challenges: compatibility, low latency, and low power consumption. Keywords: Bluetooth HID, USB HID, Virtual Cable.
Bluetooth HID Technical Specification Snapshot
| Parameter | Description |
|---|---|
| Protocol Category | Bluetooth HID Profile |
| Reference Foundation | USB HID Specification |
| Typical Languages | C, C++, embedded firmware |
| Core Transport Layer | L2CAP |
| Service Discovery | SDP |
| Typical Devices | Keyboards, mice, remote controls, game controllers |
| Key Mechanisms | Report, Boot Protocol, Virtual Cable, Sniff |
| Star Count | Not provided in the source content |
| Core Dependencies | Bluetooth controller, HID class driver, L2CAP, SDP, GAP |
Bluetooth HID Essentially Inherits and Adapts USB HID for the Wireless World
Bluetooth HID does not reinvent the input protocol. Instead, it carries the mature USB HID model onto a wireless link. The biggest advantage of this approach is that hosts can continue to reuse existing HID class drivers, which reduces the cost of building a separate driver for each peripheral type.
The most important capability of USB HID is self-description. A device tells the host what type of device it is, what data it sends, and what each byte means through descriptors. Bluetooth HID preserves this mechanism, which allows keyboards, mice, and game controllers to connect to the system in a unified way.
The Difference Between Bluetooth HID and USB HID Lies in the Wireless Adaptation Layer
Wired USB depends on a physical cable, which is stable and offers sufficient power. Bluetooth, by contrast, must deal with discovery, pairing, interference, and battery life. As a result, Bluetooth HID introduces additional mechanisms such as Virtual Cable, dual-channel communication, SDP-based discovery, and low-power modes to simulate an experience that feels as reliable as plugging in a cable.
// Pseudocode: The host parses an input report based on the descriptor
void handle_hid_report(uint8_t *report, Descriptor *desc) {
Field x = parse_field(desc, "X"); // Parse the X-axis field definition
Field y = parse_field(desc, "Y"); // Parse the Y-axis field definition
int dx = extract_value(report, x); // Extract X displacement from the report
int dy = extract_value(report, y); // Extract Y displacement from the report
update_cursor(dx, dy); // Update the host cursor position
}This code shows how the host relies on the report descriptor to understand the semantic meaning of data reported by the device.
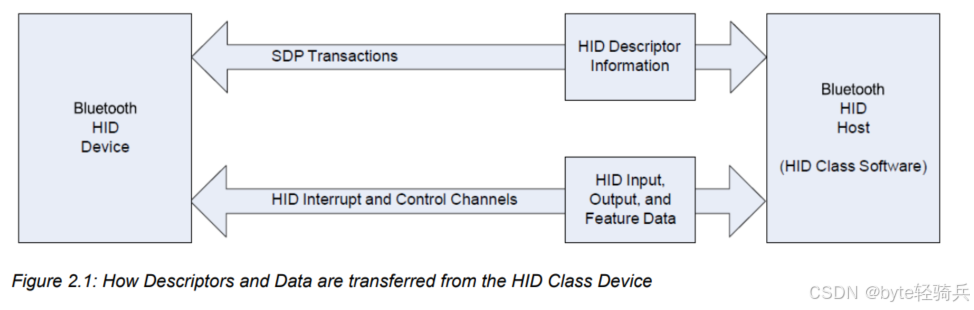
Descriptors and the Report System Together Form the Data Core of Bluetooth HID
Descriptors serve as the protocol entry point, while reports carry runtime data. The host first parses descriptors and then correctly processes subsequent input, output, and feature reports. Their responsibilities are clearly separated: descriptors define the rules, and reports carry the interaction payload.
The most important descriptor is the report descriptor. It defines the field layout, length, range, and purpose of input reports, output reports, and feature reports. The host does not need a proprietary driver. As long as it can parse the report descriptor, it can understand device behavior.
Input, Output, and Feature Reports Each Serve a Distinct Role
Input reports travel from the device to the host and carry dynamic data such as keystrokes, displacement, joystick values, and sensor readings. They emphasize low latency and are typically sent asynchronously when the device state changes.
Output reports travel from the host to the device and control LEDs, vibration, motors, or mode switching. Feature reports are primarily used for configuration and queries, such as DPI, firmware version, sensitivity, and other non-real-time parameters.
// Pseudocode: The device sends a mouse movement input report
typedef struct {
uint8_t buttons; // Mouse button state
int8_t x; // X-axis displacement
int8_t y; // Y-axis displacement
} MouseInputReport;
void send_mouse_move(int8_t dx, int8_t dy) {
MouseInputReport rpt = {0};
rpt.x = dx; // Write the X-direction delta
rpt.y = dy; // Write the Y-direction delta
hid_interrupt_send((uint8_t *)&rpt, sizeof(rpt)); // Send with low latency through the interrupt channel
}This code illustrates how an input report sends real-time interaction data to the host in a compact format.
Dual Protocol Modes Balance Advanced Capabilities with Basic Compatibility
Bluetooth HID defines Report Protocol Mode and Boot Protocol Mode. The former is the full-featured mode, while the latter is the compatibility mode. Their coexistence is fundamentally designed to support both feature-rich devices and resource-constrained hosts.
Report Protocol Mode depends on report descriptors and supports complex devices with multiple axes, many buttons, and custom functions. Game controllers, professional control devices, and composite input devices typically operate in this mode.
Boot Mode Allows Basic Input Devices to Work Even in Early System Environments
Boot Protocol Mode uses a fixed format and does not require the host to parse complex descriptors. This allows keyboards and mice to provide basic input in BIOS environments, embedded boot stages, or simplified host systems.
A common approach is for the device to use Boot Mode during early system initialization, then switch to Report Mode after the operating system loads the full HID class driver, thereby enabling all available functionality.
// Pseudocode: Switch protocol modes based on the host request
void on_set_protocol(uint8_t mode) {
if (mode == 0) {
current_mode = BOOT_PROTOCOL; // Switch to Boot Protocol Mode
} else {
current_mode = REPORT_PROTOCOL; // Switch to full Report Protocol Mode
}
}This code reflects how the host can dynamically choose the protocol complexity it needs.
The Bluetooth HID Software Stack Uses L2CAP and SDP for Discovery, Connection, and Transport
The Bluetooth HID software stack can be divided into the application layer, the HID service layer, the Bluetooth protocol layer, and the controller layer. On the device side, firmware collects input and generates reports. On the host side, the stack parses reports and dispatches events. At the lower layers, L2CAP, SDP, and GAP provide transport and discovery.
L2CAP serves as the bearer layer and maps HID control signaling and interrupt data to logical channels. SDP exposes the device’s HID capabilities. GAP handles access states such as discoverability and connectability.
 AI Visual Insight: This diagram presents the layered structure of the core Bluetooth HID components, with emphasis on the dependency relationships among the report system, protocol modes, and software stack. It helps explain the overall architecture: descriptors define the data, protocols determine compatibility, and the software stack makes the system work in practice.
AI Visual Insight: This diagram presents the layered structure of the core Bluetooth HID components, with emphasis on the dependency relationships among the report system, protocol modes, and software stack. It helps explain the overall architecture: descriptors define the data, protocols determine compatibility, and the software stack makes the system work in practice.
A Single Mouse Movement Traverses the Entire Protocol Stack
After the device detects movement, firmware generates an input report. The HID service passes it to the L2CAP interrupt channel. The controller sends it over the wireless link. The host-side protocol stack receives it and passes it to the HID class driver. Finally, the operating system updates the cursor position.
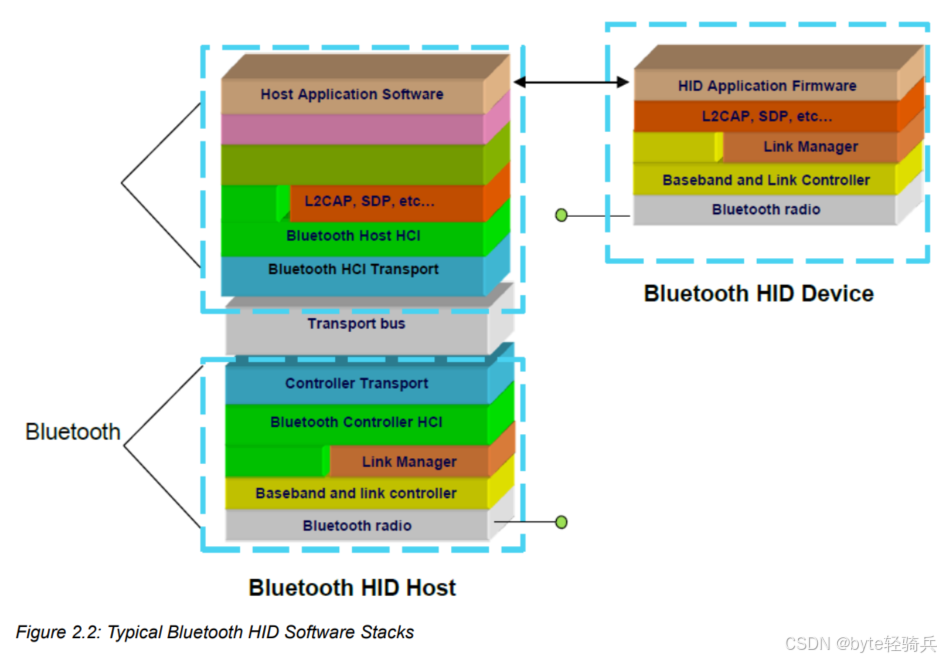 AI Visual Insight: This diagram shows the symmetric software stack structure on both the host and device sides, typically including the application layer, HID layer, L2CAP/SDP layer, HCI, and the controller layer. It clearly illustrates the full path from sensor acquisition to the host input subsystem.
AI Visual Insight: This diagram shows the symmetric software stack structure on both the host and device sides, typically including the application layer, HID layer, L2CAP/SDP layer, HCI, and the controller layer. It clearly illustrates the full path from sensor acquisition to the host input subsystem.
The Virtual Cable Mechanism Is the Key to Simulating USB-Style Exclusive Attachment in Bluetooth HID
A wireless environment has no physical cable, so Bluetooth HID introduces Virtual Cable. It logically establishes an exclusive relationship in which one device binds to one host, preventing multiple hosts from competing for the same input stream.
Virtual Cable has three key characteristics: exclusivity, persistence, and detachability. Exclusivity ensures a single connection target. Persistence ensures that pairing and configuration can be stored. Detachability allows users to explicitly break or rebuild the binding, much like unplugging and reconnecting a USB cable.
The Association Process Determines Whether the Host Can Reliably Take Ownership of the Device
During first-time use, the device enters discoverable mode. The host scans for it, reads its SDP record, and completes pairing, bonding, and establishment of the dual L2CAP channels. After that, both sides store addresses, keys, and configuration so they can reconnect directly the next time.
// Pseudocode: First-time association and Virtual Cable establishment flow
void start_association(void) {
enable_discoverable(true); // Allow the host to discover the device
wait_for_pairing(); // Wait for the host to complete pairing
save_link_key(); // Save the key to avoid repeated pairing later
create_hid_control_channel(); // Create the control channel
create_hid_interrupt_channel(); // Create the interrupt channel
}This code summarizes the minimum closed loop from discovery to a usable Bluetooth HID connection.
Low-Power Management Is a Critical Engineering Priority in Bluetooth HID Design
For battery-powered devices such as keyboards, mice, and remote controls, power efficiency directly determines product usability. Bluetooth HID typically relies on Sniff and Sniff Subrating to reduce the active duty cycle while idle and restore responsiveness quickly when interaction occurs.
Its core strategy is not to remain in low-power mode at all times, but to wake on demand. When there is no user activity, the device lengthens the listening interval. When input occurs, it shortens the interval immediately. This creates a practical balance between power consumption and latency.
Power Optimization Must Be Designed Together with the Device Type
Keyboards prioritize wake-up speed. Mice prioritize motion continuity. Remote controls care more about standby duration. In real products, engineers usually need different Sniff parameters, LED strategies, and auto-sleep timing for different peripherals.
Developers Should Understand Bluetooth HID as a Compatibility-First Wireless Input Framework
From an engineering perspective, the success of Bluetooth HID does not come from protocol complexity. It comes from moving the mature USB HID ecosystem into the wireless domain. Descriptor reuse solves driver adaptation. Dual protocol modes solve compatibility. Virtual Cable solves connection semantics. Low-power mechanisms solve battery life.
If you are building a keyboard, mouse, remote control, or gaming peripheral, understanding these four keywords is enough to form a solid mental model: descriptors, reports, Virtual Cable, and low power.
FAQ
FAQ 1: Why Doesn’t Bluetooth HID Define a Completely New Protocol?
Because the USB HID ecosystem is already mature, and hosts already provide generic drivers. Reusing the descriptor and report mechanisms significantly reduces device development cost, host adaptation effort, and interoperability overhead.
FAQ 2: How Should You Choose Between Boot Protocol and Report Protocol?
Use Boot Mode first for basic keyboards and mice, BIOS scenarios, or resource-constrained environments. Use Report Mode when you need advanced capabilities such as multimedia keys, custom buttons, or gamepad axis data.
FAQ 3: What Are the Most Common Issues When Debugging Bluetooth HID Products?
The most common issues are incorrect report descriptors, failures during L2CAP channel establishment, unstable reconnection strategies, and overly aggressive low-power settings, all of which can lead to poor compatibility, high latency, or abnormal power consumption.
AI Readability Summary
This article systematically reconstructs the underlying design logic of Bluetooth HID architecture. It focuses on USB HID reuse, the report system, dual protocol modes, the L2CAP/SDP software stack, Virtual Cable, association, and low-power management, helping developers quickly build a complete understanding of wireless human interface protocols.