[AI Readability Summary] Elastic introduced a unified API key for Elastic Cloud Serverless, allowing developers to use a single credential to manage organization resources and access Elasticsearch and Kibana APIs. This removes the split between control plane and data plane credentials in CI/CD workflows and reduces key sprawl, rotation overhead, and fragmented auditing. Keywords: Elastic Cloud, Serverless, API Key.
Technical specifications show the core capabilities at a glance
| Parameter | Details |
|---|---|
| Product/Platform | Elastic Cloud Serverless |
| Core capability | Unified authentication for Cloud, Elasticsearch, and Kibana APIs |
| Architecture keywords | Globally distributed IAM, regional local validation, dynamic role mapping |
| Interface protocol | HTTPS REST API |
| Authentication method | Authorization: ApiKey |
| Languages/Invocation methods | curl, JSON, any HTTP-capable language |
| Star count | Not provided in the original source |
| Core dependencies | Elastic Cloud API, Elasticsearch Serverless API, Kibana API |
The unified API key directly eliminates credential sprawl in Serverless automation
Previously, Elastic’s identity model was split into two layers: the Cloud API key handled the control plane, while the Elasticsearch API key handled the data plane. As organizations grew, this design quickly amplified operational complexity, especially in Terraform, GitOps, and CI/CD pipelines.
Typical issues included creating a project and then generating another project-level key, injecting that second credential into downstream services, rotating each key separately, and auditing them independently. The result was uncontrolled credential growth, slower troubleshooting, and delayed access revocation.
The traditional two-key model slows down delivery efficiency
When the control plane and data plane are separated, a complete automation flow must cross two different authorization boundaries. For SRE teams, this is not just one extra step—it makes the entire pipeline more fragile.
# The traditional model usually requires two-stage authentication
curl -H "Authorization: ApiKey $CLOUD_KEY" \
https://api.elastic-cloud.com/api/v1/serverless/projects
# Then generate or inject an Elasticsearch project-level key for a specific project
curl -H "Authorization: ApiKey $ES_PROJECT_KEY" \
https://YOUR_ES_ENDPOINT/_queryThis flow shows the core problem: project creation and data access depend on different credentials, which makes automation inherently more complex.
The new unified authentication model lets one key cover both control and data access
Now, an Elastic Cloud API key in Serverless environments can be granted permissions for Cloud, Elasticsearch, and Kibana APIs. That means the same credential can manage organization resources while also performing queries, ingestion, and alerting-related operations.
The key change is not simply one fewer key. The real improvement is unified identity governance. Audit logs can trace activity around a single credential, while rotation and revocation become single-point operations instead of a coordinated process across multiple systems.
Unified access does not mean unlimited privilege
Elastic uses role_assignments and application_roles to control scope. You can bind the same key only to specific projects and roles, such as read-only or administrator access, to limit the blast radius of credential exposure.
{
"description": "unified-automation-key",
"expiration": "90d",
"role_assignments": {
"project": {
"elasticsearch": [
{
"role_id": "elasticsearch-admin",
"organization_id": "YOUR_ORG_ID",
"all": false,
"project_ids": ["YOUR_PROJECT_ID"],
"application_roles": ["admin"]
}
]
}
}
}This configuration shows the essence of the unified key model: project-level role constraints are attached to an organization-level credential.
Programmatic creation of unified keys is ready for direct pipeline integration
The Elastic Cloud API now supports programmatic creation of unified keys. For platform engineering teams, this means credential generation, expiration policies, and role assignments can be built into standardized release workflows.
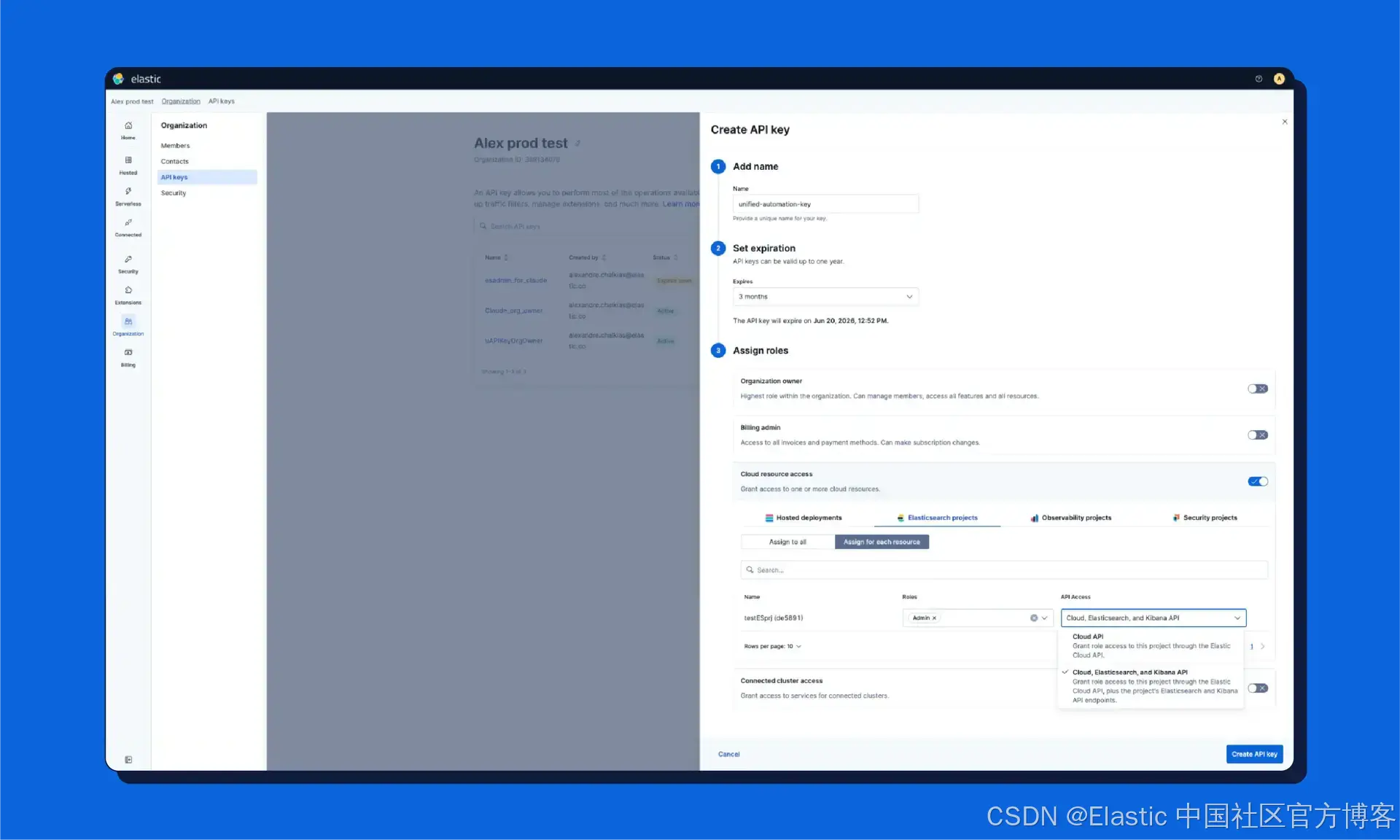 AI Visual Insight: This interface shows the configuration entry point in the Elastic Cloud console for assigning Cloud, Elasticsearch, and Kibana permissions to an API key. The key takeaway is that role-based authorization has expanded from the control plane into the Serverless data plane, turning unified authentication into a visual permission orchestration capability.
AI Visual Insight: This interface shows the configuration entry point in the Elastic Cloud console for assigning Cloud, Elasticsearch, and Kibana permissions to an API key. The key takeaway is that role-based authorization has expanded from the control plane into the Serverless data plane, turning unified authentication into a visual permission orchestration capability.
curl -X POST \
-H "Content-Type: application/json" \
-H "Authorization: ApiKey $EC_API_KEY" \
"https://api.elastic-cloud.com/api/v1/users/auth/keys" \
-d '{
"description": "unified-automation-key",
"expiration": "90d",
"role_assignments": {
"project": {
"elasticsearch": [
{
"role_id": "elasticsearch-admin",
"organization_id": "YOUR_ORG_ID",
"all": false,
"project_ids": ["YOUR_PROJECT_ID"],
"application_roles": ["admin"]
}
]
}
}
}'This command creates a unified API key that can access both Elastic Cloud and Elasticsearch Serverless.
After creation, the same Authorization: ApiKey header can be used for both api.elastic-cloud.com and the corresponding Elasticsearch Serverless endpoint, significantly reducing credential distribution overhead.
The underlying capability comes from a globally distributed identity layer, not simple token reuse
The main challenge here is not the UI—it is authentication latency. Historically, Cloud API keys were stored in a centralized global security cluster, which worked for the control plane but was not suitable for high-frequency, low-latency data queries.
To solve this, Elastic introduced a globally distributed IAM data layer and regional local authentication services. As a result, search and ingestion requests can be validated within the local region without returning to the global control plane.
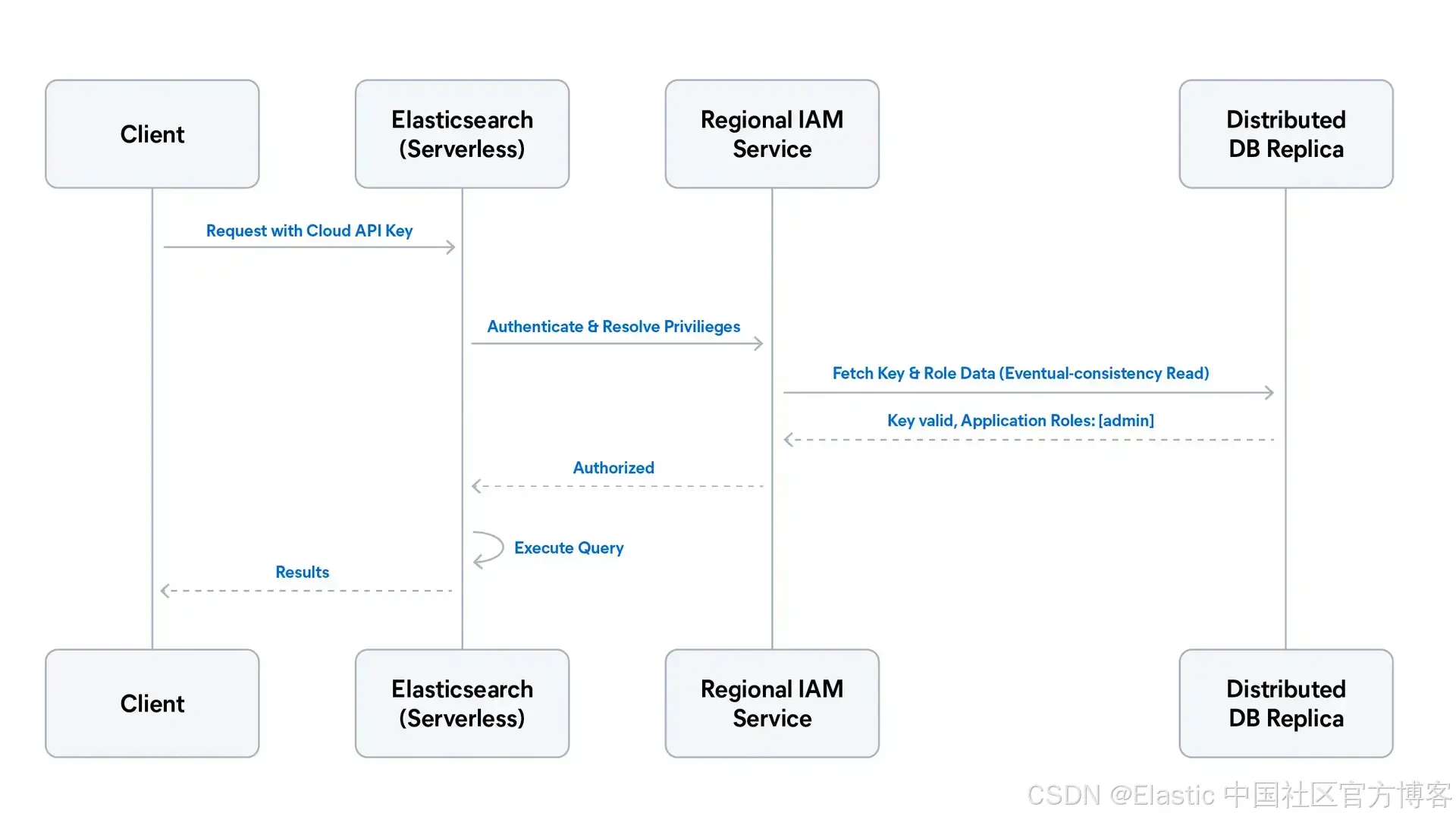 AI Visual Insight: This sequence diagram shows the authentication path between the client, Elasticsearch, the regional IAM service, and the globally distributed database. The critical technical detail is that authentication is validated in the local region, while role resolution comes from IAM data synchronized to local replicas. This preserves low latency and reduces runtime dependency on the global control plane.
AI Visual Insight: This sequence diagram shows the authentication path between the client, Elasticsearch, the regional IAM service, and the globally distributed database. The critical technical detail is that authentication is validated in the local region, while role resolution comes from IAM data synchronized to local replicas. This preserves low latency and reduces runtime dependency on the global control plane.
Distributed IAM solves three core problems
First, identity data is persisted in a globally highly available database to ensure multi-region synchronization. Second, regional IAM validates keys against local replicas to reduce authentication latency. Third, Cloud-layer roles are dynamically mapped to native Elasticsearch privileges, removing dependency on the local .security index.
Client request -> Regional Elasticsearch
-> Regional IAM validates the API key
-> Local replica resolves roles
-> Elasticsearch executes authorization and query
-> Return resultsThis path shows that the key to unified authentication is regionalized local authorization, not simply sharing the same credential.
This unified identity model also lays the foundation for cross-project search
The strategic value of unified identity is that it turns cross-project access control into a platform capability. Future Cross-Project Search can securely propagate the same identity context across multiple Serverless projects without requiring complex inter-project trust configuration.
This matters especially for teams managing observability, security, and business search data at the same time. A unified key allows the system to evaluate an operator’s permissions across multiple projects automatically, reducing certificates, duplicate credentials, and manual integration work.
Developers should focus first on permission boundaries and scope of applicability
This capability currently targets Elastic Cloud Serverless. The original source specifically notes that in Elastic Cloud Hosted environments, Cloud API keys still primarily serve control plane management, while broader support for hosted cluster APIs remains on the roadmap.
The best practice is to start by using unified keys for Serverless automation, audit consolidation, and rotation simplification, then gradually refine role scopes on a per-project basis. Do not misinterpret unified access as a universal super-admin key.
FAQ
1. What is the fundamental difference between the unified API key and the original Elasticsearch API key?
The unified API key is an extended organization-level Cloud credential that can access Cloud, Elasticsearch, and Kibana APIs at the same time. A traditional Elasticsearch API key typically works only within the data plane of a single project.
2. Does unification introduce greater security risk?
Not inherently, as long as you use role_assignments and application_roles correctly. What is unified is the credential governance entry point—not unlimited privilege. Least privilege, expiration policies, and project-scoped authorization still apply.
3. Why did Elastic implement regional IAM local validation?
Because data plane requests are extremely latency-sensitive. If every query had to return to the global control plane for key validation, latency would increase and create a single operational dependency. Regional IAM keeps authentication and authorization as local as possible while preserving both performance and availability.
Core takeaway: Elastic introduced a unified API key for Serverless environments that can access the Cloud control plane and the Elasticsearch and Kibana data planes at the same time. This significantly reduces credential sprawl, rotation complexity, and fragmented auditing. Under the hood, the model relies on globally distributed IAM and regional local validation, laying the identity foundation for future cross-project search.