This article focuses on Socket communication and the structure of UDP datagrams. It explains how hosts, IP addresses, processes, and ports identify communication endpoints, and it clarifies common misconceptions about UDP size limits and IP fragmentation so developers can design network programs correctly. Keywords: Socket, UDP, port number.
Technical Specification Snapshot
| Parameter | Description |
|---|---|
| Domain | Computer Networks / Socket Programming |
| Related Languages | Java, C, Python |
| Transport Protocols | TCP, UDP, IP |
| UDP Header Length | Fixed at 8 bytes |
| Port Number Length | 16 bits, range 0–65535 |
| Star Count | Original data not provided |
| Core Dependencies | Operating system Socket API, TCP/IP protocol stack |
Identification in network communication must be understood in layers
Network communication does not rely on a single identifier. Hosts, IP addresses, processes, ports, and sockets work together. Understanding the boundary of each object is a prerequisite for writing correct network programs.
A single host can have multiple IP addresses, and multiple processes can run on the same host at the same time. A process is a running instance of a program, and network communication ultimately terminates at a specific Socket inside a specific process.
The relationship between hosts, processes, and programs forms a mapping chain
A host carries the operating system and the network protocol stack. A process executes specific business logic, while a program is the static artifact from which the process is created. In development, you should distinguish between a program file and a running communication entity.
Host -> IP address
Host -> multiple processes
Process -> one running program instance
Process -> one or more Sockets
Socket -> binds a port to participate in communicationThis structure shows that network traffic is not delivered to a program name. It is delivered to the Socket identified by an IP address and port.
Ports and Sockets are the core entry points for transport-layer communication
A port is the network service entry point exposed by the operating system. At its core, it is a transport-layer number. A Socket is the communication endpoint that a program extends into the operating system network stack. It is the object your code actually uses to read and write network data.
A port number occupies 2 bytes, or 16 bits, and ranges from 0 to 65535. A common classification is: 0–1023 for well-known ports, 1024–49151 for registered ports, and 49152–65535 for dynamic or private ports.
The same port does not mean multiple Sockets can reuse it arbitrarily
On the same host, under the same transport protocol and the same local IP address, a local port can usually be bound exclusively by only one Socket at a time. This is the root cause of the common startup error: “Address already in use”.
# Pseudocode: demonstrate the uniqueness of port binding
import socket
s1 = socket.socket(socket.AF_INET, socket.SOCK_DGRAM) # Create a UDP Socket
s1.bind(("127.0.0.1", 8080)) # Bind the local IP address and port
s2 = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
# s2.bind(("127.0.0.1", 8080)) # Rebinding the same protocol, IP, and port usually failsThis code shows that local port binding is constrained by the protocol stack and cannot simply be duplicated.
TCP and UDP use fundamentally different Socket models
A TCP server typically creates a ServerSocket or listening Socket first, binds it to a port, and then calls accept to receive connections. For each client that connects, the kernel returns a new connected Socket for long-lived communication with that client.
These TCP connections are not distinguished by the server port alone. They are identified by a more complete connection key, commonly understood as a five-tuple: source IP, source port, destination IP, destination port, and transport protocol.
A UDP DatagramSocket does not establish a connection and sends or receives datagrams directly
A UDP DatagramSocket only needs to bind to a port to receive datagrams from different clients. It has no connection setup or teardown process, so it is lighter weight, but it does not guarantee reliable or ordered delivery.
DatagramSocket socket = new DatagramSocket(9090); // Bind the UDP port
byte[] buf = new byte[1024];
DatagramPacket packet = new DatagramPacket(buf, buf.length);
socket.receive(packet); // Receive one complete UDP datagram
System.out.println(packet.getLength()); // Print the length of the data received this timeThis code demonstrates the datagram-oriented nature of UDP: each receive corresponds to one complete message boundary.
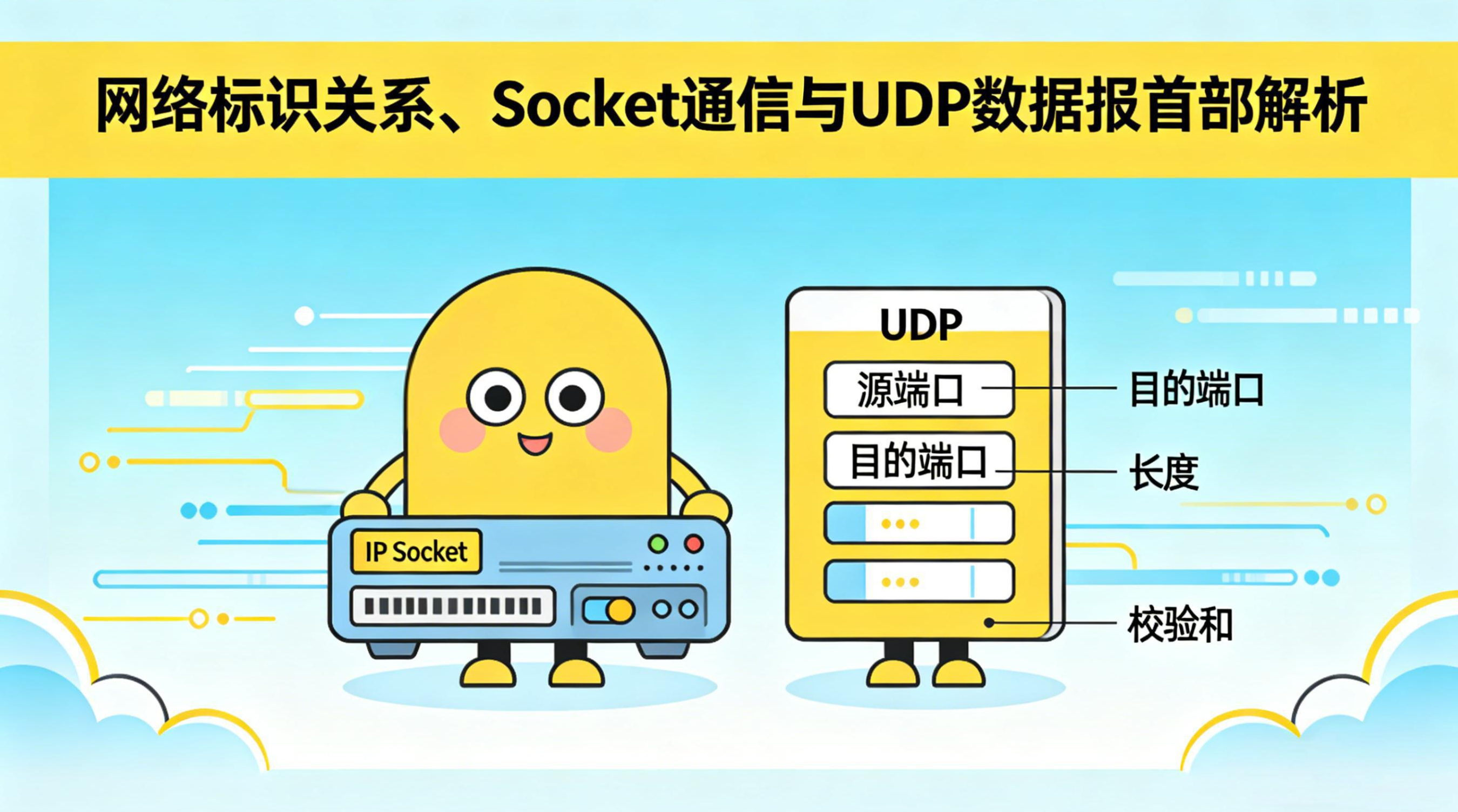
The UDP header is very small but still complete
The UDP header is fixed at only 8 bytes. It contains 4 fields, each 2 bytes long: source port, destination port, length, and checksum. The protocol is designed to be minimal, so its overhead is much smaller than TCP.
The source port tells the receiver where to send a reply, while the destination port identifies the target application. The length field represents the total length of the UDP datagram, including both the header and the payload.
The UDP length field defines the theoretical maximum, but not the practical safe send size
From the transport-layer perspective, the UDP length field is 16 bits, so the total UDP datagram size can theoretically range from 8 to 65535 bytes. After subtracting the 8-byte header, the maximum UDP payload is 65527 bytes.
However, once UDP passes the packet down to the IP layer, the packet still needs an IP header. If the IPv4 header uses the minimum size of 20 bytes, then when a single IP packet has a maximum total size of 65535 bytes, the largest UDP datagram it can carry is 65515 bytes, which means the maximum UDP payload becomes 65507 bytes.
Maximum UDP total length = 65535
Maximum UDP payload = 65535 - 8 = 65527
Maximum IP packet total length = 65535
If the IP header is at least 20 bytes:
Maximum UDP total length = 65535 - 20 = 65515
Maximum UDP payload = 65515 - 8 = 65507These numbers explain why engineering discussions often say that the safe upper bound for a UDP payload is 65507 bytes.
UDP delivers full messages while TCP delivers a byte stream
UDP is datagram-oriented. A single application-layer send corresponds to one complete message boundary. Unlike TCP, the transport layer does not merge or split application data into a boundary-free byte-stream abstraction.
If the application-layer data exceeds 65527 bytes, UDP cannot encapsulate it at the transport layer, and the send operation usually fails immediately. If the data size is between 65507 and 65527 bytes, the UDP layer may still construct the datagram, but it will often trigger fragmentation once it reaches the IP layer.
IP fragmentation increases packet loss risk
After IP fragmentation occurs, the loss of any fragment prevents the entire UDP datagram from being reassembled correctly. So even if the protocol allows large packets, production systems should still keep packet sizes under control and avoid depending on fragmentation whenever possible.
def choose_udp_payload(size):
if size > 65527:
return "UDP-layer encapsulation fails and sending raises an error" # Exceeds the theoretical UDP payload limit
if size > 65507:
return "Valid at the UDP layer, but the IP layer will likely fragment it" # Exceeds the safe IP carrying range
return "Can be sent normally, but you should still reduce it further based on MTU" # Better suited to real network transportThis logic helps you quickly judge whether a UDP payload is transmissible through the protocol stack.
The checksum detects data corruption during transmission
The UDP checksum is a 16-bit field. It covers not only the UDP header and payload, but also includes the IP pseudo-header in the calculation. This design validates part of the critical network-layer information as well and improves error-detection capability.
It can detect errors, but it cannot provide retransmission, ordering, or congestion control the way TCP does. That is why UDP is a good fit for low-latency scenarios, packet-loss-tolerant workloads, or systems where the application layer implements reliability itself.
AI Visual Insight: This image helps illustrate the topic of network communication. It typically uses a schematic representation to show hosts, protocol stacks, or packet flow. For understanding this article, you can treat it as an abstract mapping from network nodes to transport-layer endpoints rather than as an exact protocol field diagram.
The most practical conclusion in development is to control boundaries instead of memorizing definitions
When writing UDP programs, the key is not just remembering the phrase “connectionless.” The real priority is to understand three boundaries clearly: the port-binding boundary, the message boundary, and the length boundary. Many production issues come from misjudging one of these three.
If you are building log collection, LAN broadcast, real-time voice, or game state synchronization, UDP is often a strong fit. If you require reliability, ordering, and retransmission, TCP is the default solution.
FAQ
1. Why can one server port serve multiple TCP clients at the same time?
Because the listening port only accepts incoming connections. After a connection is established, the kernel creates an independent Socket for it. The kernel distinguishes each connection by the combination of source IP, source port, destination IP, destination port, and protocol.
2. Is the UDP maximum 65527 or 65507?
65527 is the theoretical maximum payload derived from the UDP length field. 65507 is the more practical upper bound for a single IP packet after accounting for the minimum 20-byte IPv4 header.
3. If UDP can send large packets, why do engineers still recommend small packets?
Because large packets can easily trigger IP fragmentation, and losing any fragment causes the entire datagram to fail. In real systems, developers also consider the MTU and keep packets smaller to reduce retransmission cost and packet-loss impact.
Core summary: This article systematically explains the mapping relationship among hosts, IP addresses, processes, ports, and Sockets. It also breaks down the UDP header fields—source port, destination port, length, and checksum—and focuses on the three critical size boundaries of 65535, 65527, and 65507, along with their relationship to IP fragmentation and TCP byte-stream semantics.