The core of Bluetooth HID system design is not just making devices connect. It is making them stable, power-efficient, and interoperable. This article focuses on four specification-driven pillars—host classification, QoS, power control, and virtual cable handling—to solve common problems such as poor compatibility, high latency, short battery life, and chaotic multi-host switching. Keywords: Bluetooth HID, QoS, Virtual Cable
Technical Specification Snapshot
| Parameter | Description |
|---|---|
| Technical Topic | Bluetooth HID System Design |
| Language | Chinese |
| Related Protocols | Bluetooth HID, L2CAP, SDP, Sniff Subrating |
| Target Devices | Keyboards, mice, remote controls, game controllers, embedded hosts |
| Star Count | Not provided in the source |
| Core Dependencies | Bluetooth protocol stack, HID Report Descriptor, L2CAP, ACL link |
Bluetooth HID system design must satisfy both compliance and user experience
Bluetooth HID is not a single-protocol problem. It is a system design problem. Whether a device is correctly recognized by the host, whether input stays low-latency, whether idle behavior saves power, and whether reconnection is fast after a disconnect are all determined by system-level rules working together.
The most common development mistake is focusing only on the report descriptor or input reporting while ignoring host capability tiers, QoS negotiation, and the virtual cable lifecycle. The usual result is simple: it works in a demo, but fails in production.
Host classification defines your compatibility boundary
The specification divides hosts into General Bluetooth HID Hosts and Limited Bluetooth HID Hosts. The former targets PCs, phones, and game consoles, with an emphasis on broad compatibility. The latter targets door locks, lighting controllers, and dedicated control systems, with an emphasis on lower resource usage and tightly scoped scenarios.
A general host must support third-party application access to HID capabilities, including GET_REPORT, SET_REPORT, asynchronous input and output reports, SDP retrieval, and device reconnection event handling. It must not apply discriminatory filtering based on brand, device name, or vendor information.
// On the general host side: read SDP after connection setup,
// then decide how to parse the report protocol.
int hid_host_init(device_t *dev) {
if (!sdp_query(dev)) return -1; // Read the SDP record to obtain device capabilities
if (!parse_report_descriptor(dev)) return -2; // Parse the report descriptor and build the mapping
enable_interrupt_channel(dev); // Enable the interrupt channel to receive real-time input
return 0;
}This code reflects the minimum initialization path for a general host: discover capabilities first, parse the descriptor next, and then enter real-time communication.
Limited hosts can complete specific tasks at lower cost
A limited host may filter devices and support only predefined types. For example, a door lock may accept only keyboards, while a lighting controller may accept only remote controls. It may even omit the SDP client and establish the HID control channel directly through a fixed L2CAP PSM to reduce implementation complexity.
This class of host must support at least one report type. If it supports only the Boot Protocol, it must still guarantee asynchronous input reports. Otherwise, the basic input experience for keyboards and mice cannot be delivered.
Quality of service design directly determines the upper bound of input latency
The core HID experience is immediate feedback to user actions. In Bluetooth 2.1+EDR and later environments, QoS behavior is driven more by Sniff Subrating. In earlier versions, it depends on joint negotiation between Sniff parameters and L2CAP QoS.
The control channel is well suited for Best Effort traffic because it carries configuration and query operations. The interrupt channel should prioritize Guaranteed service because key presses, pointer movement, and vibration all belong to strongly real-time data flows.
The interrupt channel should optimize for low latency rather than high throughput
In practice, engineering should prioritize two metrics: transport latency and latency variation. Keyboards and mice typically require response times on the order of 10 ms. Force feedback and composite devices require a larger bandwidth budget.
# Generate recommended QoS parameters based on device type.
def qos_profile(device_type: str):
if device_type == "keyboard":
return {"bandwidth": 900, "latency_ms": 10, "variation_ms": 10} # Keyboard: low bandwidth, low latency
if device_type == "mouse":
return {"bandwidth": 300, "latency_ms": 10, "variation_ms": 10} # Mouse: more sensitive to jitter stability
return {"bandwidth": 1600, "latency_ms": 10, "variation_ms": 10} # Game controllers and other composite devicesThis code helps you quickly select QoS targets by device type so the protocol stack can apply the right profile automatically during initialization.
Power management should be device-led rather than host-controlled
The specification makes the Bluetooth HID device the primary owner of power management. The reason is simple: the device knows its own hardware state best. It knows when to reduce scan frequency, turn off LEDs, pause sensors, or enter deeper sleep states.
The host has a deliberately limited role: send SUSPEND when entering sleep and send EXIT_SUSPEND when resuming. Beyond that, it should not take over the device’s energy-saving logic in a heavy-handed way.
Sniff and active reconnect are the two most important power-saving layers
The first layer is Sniff or Sniff Subrating, which reduces wake frequency while keeping the connection alive. The second layer is to disconnect proactively after a long idle period, then let the device reconnect actively when the user interacts again.
For devices that declare HIDReconnectInitiate as TRUE, this model is especially valuable. It can reduce idle current to a very low level without significantly degrading wake-up responsiveness.
// Simplified example of a device-side power state machine
void hid_power_manage(bool active_event, bool host_suspend) {
if (host_suspend) enter_suspend_mode(); // Host is sleeping; enter low-power mode
else if (active_event) set_sniff_interval(10); // Input is active; shorten the interval for low latency
else set_sniff_interval(500); // Idle state; extend the interval to reduce power consumption
}This code shows how a device can switch dynamically between responsive active behavior and efficient idle behavior.
The virtual cable mechanism determines whether a wireless peripheral feels as reliable as a wired one
A virtual cable is essentially a persistent host-device binding relationship. A usable connection exists only when both the control channel and the interrupt channel are established successfully. At that point, the implementation should persist state such as addresses, keys, and protocol mode.
In multi-host scenarios, a device may store multiple binding records, but only one connection can be active at a time. An LRU policy is recommended to evict the least recently used host and prevent uncontrolled growth of the storage table.
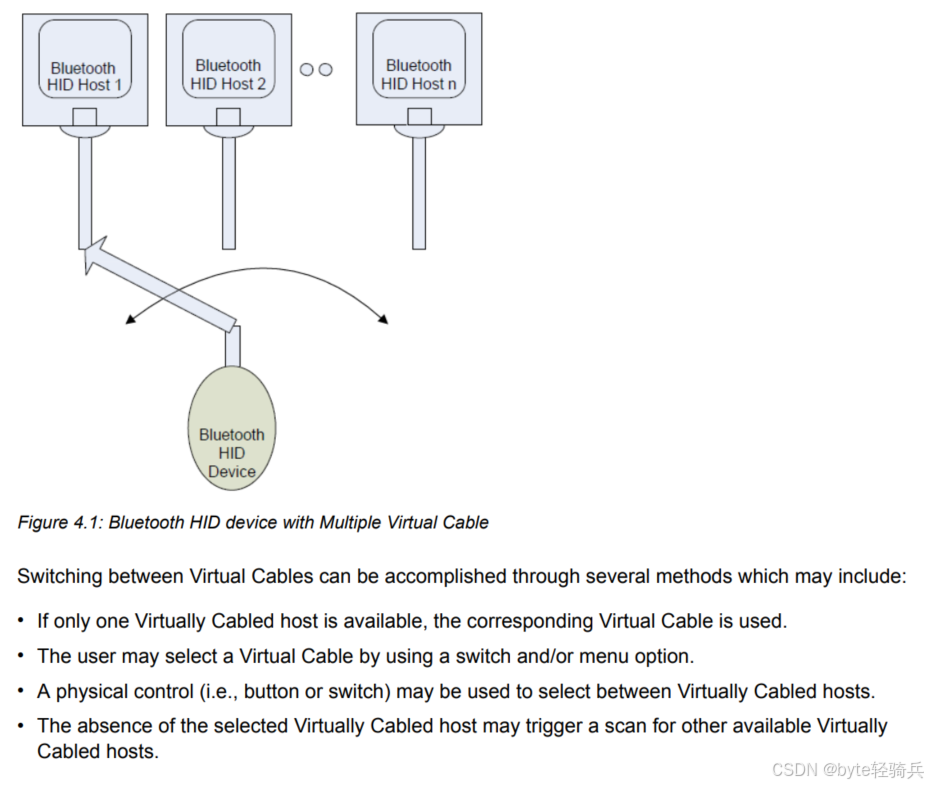 AI Visual Insight: This diagram illustrates the connection switching model for a Bluetooth HID device in a multi-host environment. The key constraint is persistent storage for multiple virtual cables combined with exactly one active transport link at any given time. In implementation, you typically need to maintain the host pairing table, recency order, current ACL/L2CAP active state, and user-triggered switching events together.
AI Visual Insight: This diagram illustrates the connection switching model for a Bluetooth HID device in a multi-host environment. The key constraint is persistent storage for multiple virtual cables combined with exactly one active transport link at any given time. In implementation, you typically need to maintain the host pairing table, recency order, current ACL/L2CAP active state, and user-triggered switching events together.
Active unpairing and passive disconnects must be handled separately
An active disconnect is a Virtual Cable Unplug operation, which means a full unbinding. Both sides must delete persistent information, including pairing keys, configuration, and cached state. The next connection must go through pairing again.
A passive disconnect is usually triggered by distance, interference, or host shutdown. In this case, the binding information must not be deleted. The device or host should later be allowed to reconnect automatically according to the existing policy.
// Active virtual cable unplug flow
void virtual_cable_unplug(peer_t *peer) {
send_vcu(peer); // Send the unbind control command
delete_link_key(peer); // Delete the pairing key
clear_persistent_state(peer); // Clear the virtual cable and cached state
disconnect_interrupt(peer); // Disconnect the interrupt channel first
disconnect_control(peer); // Then disconnect the control channel
}This code captures the critical ordering for active unbinding: send control, clear state, and then tear down the channels.
During implementation, you should inspect four high-risk issues first
First, verify that you are not designing a limited host as if it were a general host, which leads to unnecessary resource overhead. Second, make sure you validate not only connectivity, but also reconnection, wake-up behavior, and low-battery notifications. Third, confirm that you do not treat a plain L2CAP disconnect as an unbind event. Fourth, ensure that you have a state consistency mechanism for multi-host switching.
If these four problem classes are not resolved early, the product may appear stable in the lab but still fail in real user environments with high latency, weak battery life, unintended reconnections, and broken host switching.
FAQ
What is the essential difference between a general host and a limited host?
A general host emphasizes non-discriminatory compatibility and third-party extensibility, so it must support SDP and the report protocol. A limited host emphasizes a minimal implementation for a specific scenario, allows device filtering, and may omit SDP.
Why is power management for HID devices mainly handled by the device?
Because the device knows the state of key scanning, sensor sampling, LEDs, and the radio module better than the host does. That allows it to make finer-grained energy-saving decisions. The host is responsible only for conveying system power state through SUSPEND and EXIT_SUSPEND.
Why must active unpairing and ordinary disconnects not be mixed?
Active unpairing deletes keys and virtual cable information, so the next connection requires pairing again. An ordinary disconnect only breaks the link while preserving state, with the goal of seamless recovery. Mixing the two directly breaks the user reconnection experience.
Core summary
This article reconstructs four critical dimensions of the Bluetooth HID system specification: host classification, QoS, power management, and virtual cable handling. It explains the capability boundaries between general and limited hosts, low-latency transport parameters, Sniff/Subrating power-saving strategies, and multi-host switching and unbinding flows to help developers satisfy interoperability, battery life, and user experience at the same time.