For high-sensitivity industries such as Xinchuang, finance, and telecommunications, Full Disk Encryption (FDE) prevents low-level data leakage caused by lost laptops, removed hard drives, device repair, and media retirement. Its core strengths are sector-level encryption and centralized key management, which close the gaps left by traditional file encryption. Keywords: Full Disk Encryption, Xinchuang Security, Data Loss Prevention.
The technical specification snapshot is outlined below
| Parameter | Details |
|---|---|
| Solution Name | Shenxinda FDE Full Disk Encryption |
| Target Scenarios | Laptops, servers, industrial control computers, classified terminals |
| Supported Languages/Platforms | Windows, Linux, Xinchuang platforms |
| Core Mechanism | Kernel-level disk filter driver, sector-level environment encryption |
| Management Model | Enterprise-grade centralized policies, unified key management |
| Comparison Target | Microsoft BitLocker |
| License/Authorization | No open-source license disclosed in the article; commercial solution |
| GitHub Stars | Not applicable; not a public open-source project |
| Core Dependencies | Windows/Linux kernel drivers, key management platform |
Physical loss of device control is the highest-risk entry point for endpoint data leaks
In Xinchuang and financial environments, an endpoint is not just a work device. It is part of the data boundary itself. A stolen laptop, a server drive removed from the chassis, an industrial control machine sent for repair, or retired storage media changing hands can all cause physical control to fail before logical access controls ever come into play.
The original examples all lead to the same conclusion: if the drive is not encrypted, an attacker does not need to log in to the system or bypass application permissions. They can simply mount the disk directly or use recovery tools to extract plaintext data. This risk directly threatens customer information, transaction records, source code, and confidential documents.
The following checklist helps identify typical risks
# Determine whether an endpoint faces high physical data exposure risk
# 1. Is the device frequently carried offsite, stationed externally, or used during business travel?
# 2. Is there a unified encryption policy before drive retirement or repair?
# 3. Is the system disk included in the encryption scope?
# 4. Does protection remain effective in offline scenarios?
# 5. Are keys centrally managed by the enterprise?This checklist helps quickly determine whether an enterprise endpoint has a structural risk where losing the device immediately means leaking the data.
Traditional file-level and partition-level solutions cannot cover low-level data exposure paths
Many enterprises have already deployed file encryption, access control, auditing, or partition protection. However, most of these solutions operate at the application layer or file system layer. They work well for daily collaboration, but they are much less effective against drive removal and offline recovery.
File-level encryption protects file objects, not the entire storage medium. Partition encryption often misses the system disk, swap space, free sectors, and deleted remnants. Once an attacker obtains the physical disk, they may still recover business data from areas that were never covered.
Application-layer controls fail once a drive is removed
risk_points = [
"File permissions depend on operating system identity", # After drive removal, the identity model no longer applies
"Folder encryption does not cover free sectors", # Deleted data may still be recoverable
"Logs and caches may retain sensitive information", # Temporary files are often overlooked
"Offline scenarios lack policy delivery capabilities" # Protection can easily degrade when disconnected
]
for item in risk_points:
print(item)This code summarizes four failure points in traditional protections under physical loss-of-control scenarios.
The core value of Full Disk Encryption is that it pushes protection down to the sector layer
The FDE approach described here does not focus on encrypting individual files. It focuses on turning the entire disk runtime environment into an encrypted space. Its technical path relies on a Windows/Linux kernel-level disk filter driver that transparently encrypts disk sectors.
This means file formats, application access patterns, and business workflows do not need to change, while data written to disk always remains encrypted at rest. Without the key, the disk cannot be mounted normally, and professional recovery tools cannot directly reconstruct readable content.
 AI Visual Insight: This image emphasizes that losing a device does not mean losing only hardware. Technically, the endpoint itself has become part of the data boundary. For high-sensitivity industries, once physical media leaves controlled custody, an unencrypted drive can directly expose customer data, business files, and source code assets.
AI Visual Insight: This image emphasizes that losing a device does not mean losing only hardware. Technically, the endpoint itself has become part of the data boundary. For high-sensitivity industries, once physical media leaves controlled custody, an unencrypted drive can directly expose customer data, business files, and source code assets.
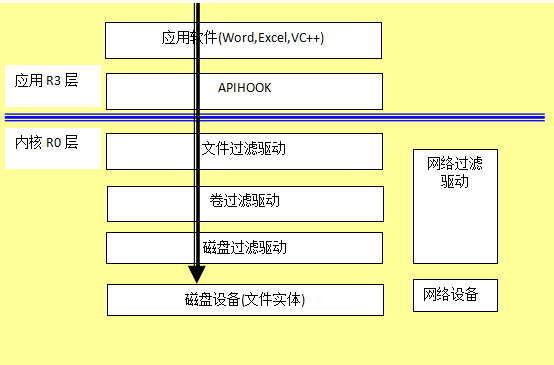 AI Visual Insight: This image illustrates the underlying Full Disk Encryption architecture. The key idea is that the driver layer intercepts disk I/O and performs transparent encryption and decryption in the sector read/write path. In practice, protection sits below the file system and application layer, which makes it much harder to bypass.
AI Visual Insight: This image illustrates the underlying Full Disk Encryption architecture. The key idea is that the driver layer intercepts disk I/O and performs transparent encryption and decryption in the sector read/write path. In practice, protection sits below the file system and application layer, which makes it much harder to bypass.
 AI Visual Insight: This image shows that after encryption, the disk remains in ciphertext form even when the drive is removed, migrated, or mounted offline. The central message is that the protected object is not a single file, but the full physical storage space and access environment of the entire medium.
AI Visual Insight: This image shows that after encryption, the disk remains in ciphertext form even when the drive is removed, migrated, or mounted offline. The central message is that the protected object is not a single file, but the full physical storage space and access environment of the entire medium.
The Full Disk Encryption workflow can be abstracted as follows
The endpoint initiates disk read/write operations
↓
The kernel filter driver intercepts I/O
↓
Before write, data is transparently encrypted by sector # Plaintext is never written directly to disk
↓
Ciphertext data is stored on disk long-term
↓
After valid boot and authentication, data is transparently decrypted for readingThis flow shows the basic operating model of Full Disk Encryption: transparent to the user, but enforced at the storage medium level.
Enterprise-grade solutions differ most in centralized control and Xinchuang compatibility
If you discuss only local encryption capability, many products can cover part of the problem. But in real government and enterprise deployments, the priorities are unified policy control, large-scale operations, key escrow, offline availability, and cross-platform consistency.
The article compares FDE with BitLocker and highlights enterprise capability differences. The former emphasizes centralized private key control, compatibility with Windows, Linux, and Xinchuang platforms, remote secure decryption, and localized support. The latter is generally a better fit for a Windows-only ecosystem or individual use cases.
The following five capabilities should be validated first during product evaluation
encryption_scope: "Does it cover the system disk and all sectors?" # Prevents protecting only data disks
key_management: "Does it support enterprise-wide centralized key escrow?" # Reduces the risks of fragmented per-device management
platform_support: "Is it compatible with Windows/Linux/Xinchuang?" # Supports heterogeneous endpoints
offline_security: "Does protection remain effective when offline?" # Meets the needs of onsite work and business travel
ops_console: "Does it provide centralized policies and status visibility?" # Supports large-scale deploymentThis configuration checklist can be used directly as an evaluation framework during an enterprise proof of concept or procurement process.
Full Disk Encryption has become foundational infrastructure for highly regulated industries
For finance, telecommunications, energy, manufacturing, and classified organizations, Full Disk Encryption is not an optional security add-on. It is part of the endpoint security baseline. It addresses one of the most easily overlooked yet most expensive physical data exposure risks.
If enterprise endpoints are used for offsite work, R&D field assignments, device repair, or asset retirement, then not deploying Full Disk Encryption means leaving the final line of defense to chance. Compared with post-incident accountability, turning the disk into unreadable ciphertext in advance is lower cost and far more controllable.
FAQ
Q: What is the fundamental difference between Full Disk Encryption and file encryption?
A: File encryption protects file objects and is often constrained by application-layer and file-system boundaries. Full Disk Encryption protects the entire sector space of the storage medium, including the system disk, caches, and residual deleted data, making it better suited to defending against drive removal and offline recovery.
Q: Why do Xinchuang and financial industries need Full Disk Encryption more than ordinary enterprises?
A: These industries commonly handle customer privacy, transaction data, source code, or classified materials, and they face stricter compliance requirements. If a device is lost, repaired, or retired improperly, the cost of exposure is far higher than in typical office scenarios.
Q: Isn’t BitLocker enough? Why consider enterprise-grade FDE?
A: If your environment is Windows-only and the management scale is limited, BitLocker can meet baseline requirements. But for heterogeneous endpoints, Xinchuang compatibility, centralized key management, offline policy enforcement, and localized operations support, enterprise-grade FDE is a better fit for large-scale government and enterprise deployments.
Core summary
For high-sensitivity industries such as Xinchuang, finance, and telecommunications, this article reconstructs the technical logic behind Full Disk Encryption. It explains why file-level and partition-level protections cannot cover physical exposure scenarios such as drive removal, repair, and retirement, and it outlines Shenxinda FDE’s sector-level encryption, centralized control, and cross-platform compatibility.